Courses
Discover thousands of courses from top institutions and platforms worldwide
Level
Course Type
Duration

Udemy
AD DS components: domain controllers, global catalog, cloning domain controllers, operations masters (FSMO), and more... What you'll learn: What is a domain controller?What is a global catalog?What are operations masters?Transferring and seizing FSMO rolesDeploying a domain controllerCloning domain controllersManaging domain controllers with PowershellPowershell Key Concepts This course is aimed to IT Pros and is supposed to give the viewer the information they need to know to get started with Active Directory (AD DS) and its key concepts. The goal is to provide coverage of ADDSmain concepts like AD DS components: domain controllers, global catalog, cloning domain controllers, operations masters (FSMO), and more...The course is targeted to help learning Active Directory and do your job more efficiently.After completing this course, you will be able to describe:What is a domain controller?What is a global catalog?Give an overview of domain controller SRV recordsAD DS sign-in processWhat are operations masters?Transfer and seize FSMO rolesDeploy a domain controllerInstall a domain controller from Server ManagerInstall a domain controller on a Server Core installation of Windows Server Install a domain controller by installing from mediaClone domain controllersAdd Another domain controllersPowershell Key ConceptsInstall a domain controller and manage FSMO roles with Powershell

YouTube
Explore advanced Active Directory (AD) attack techniques and operational security in this comprehensive conference talk from Hack In The Box Security Conference. Delve into the world of AD abuse primitives and learn how adversaries chain these techniques to form attack paths that compromise entire enterprise networks. Examine four real-world attack paths, including new abuse primitives such as diamond tickets, U2U tickets, and Shadow Credentials. Gain insights into the methodology behind successful AD attacks, including enumeration, tactical considerations, and evasion of blue team detection. Watch video demonstrations from an adversary's perspective using a Command and Control (C2) framework for a realistic offensive operation experience. Understand the root causes, implementation methods, and operational guidance for each attack path, enhancing your knowledge of AD security vulnerabilities and defense strategies.

YouTube
Learn how to perform file input/output operations in C# with this comprehensive tutorial video. Explore techniques for manipulating directories, reading and writing files, obtaining file information, utilizing FileStream, StreamWriter, BinaryWriter, and BinaryReader. Follow along with practical examples and gain hands-on experience in file handling within C# programming. Take notes using the provided cheat sheet and enhance your understanding of essential file I/O concepts for effective C# development.
Polimi OPEN KNOWLEDGE
This course introduces the key theories, concepts, models and approaches related to Production and Logistics Systems.

Udemy
Informatica Data Direction Application configuration & usage , Integration with Informatica Master Data Management (MDM) What you'll learn: IDD Subject Area BasicsDetailed view of IDD Configuration ManagerCreate Subject Area, Subject Area Child and Grand ChildDetailed view of IDD ApplicationConfigure InternationalizationUnderstanding Properties files The overview of the Informatica Master Data Director course is for beginners who would like to start their career as MDM Developer or IDD Developer. The course focuses on various features of Informatica Data Director and how to configure it in simple steps.At the end of this course, you should be able to -Access Data Director Configuration Manager, IDD ApplicationUnderstand IDD Concepts - Subject Areas and Subject Area GroupsPerform ORS BindingConfigure Subject Areas and Subject GroupsConfigure children and Grand ChildrenConfigure Cleansing and ValidationsSearch records using IDD ApplicationCreate basic and advanced searchesCreate and Update EntitiesExport and Import IDD ApplicationUnderstand configuration files

YouTube
Learn how to effectively educate and engage a board of directors on cybersecurity matters in this informative conference talk from the Central Ohio InfoSec Summit 2016. Explore the critical role of board members in overseeing organizational security, including their responsibilities, governance duties, and the importance of transparency. Discover strategies for communicating security and business value, implementing a comprehensive approach to enterprise risk management, and addressing legal implications. Gain insights into handling breaches, managing outsourcing risks, and preparing for unplanned events. Examine the challenges of educating developers, mitigating insider threats, and establishing proper governance structures. Delve into topics such as incident response, systemic escalation, and the composition of an effective board. Equip yourself with the knowledge to bridge the gap between cybersecurity professionals and board members, ensuring a strategic direction that aligns with business objectives and protects valuable assets.

Udemy
Active Directory services : Active Directory DS, Active directory GPO, Active directory DNS, Active Directory PS & many. What you'll learn: Will get expertise on operations of Active Directory components such as :-Active Directory Management ToolsActive Directory Administrative CenterActive Directory Users & ComputersActive Directory Group Policy ObjectsActive Directory Sites and ServicesActive Directory DNSActive Directory Backup and RestorePlanning Domain ControllerActive Directory PowerShell This course is build for novice employees to professionals.The course of contents are :Active Directory sites and servicesActive Directory management toolsActive Directory Users and Computers Active Directory Administrative CenterActive Directory DNSActive Directory and Group Policy ObjectActive Directory Backup &RestoreActive Directory PowerShell Windows Server Active Directory is very much indeed a important subject in Windows Server administration. In this course I have tried my best to cover all components of Active Directory. Active Directory networking and maintenance is a really important work for a system administrator's day to day job life. Active Directory is not only about managing users and computers in an organisation, it is an art for a system administrator how the he/she built a secure network to protect company's inside informations, from malicious users.In this course I have covered Active Directory administration for operating systems such asWindows Server 2019 Active Directory PowerShellWindows Server 2016 Active DirectoryWindows Server 2012/2012R2 Active Directory

Udemy
In a technological advancing industry. What you'll learn: Define the Airport Environment and Organizations that Operate within the Industry.Identify the differences between the Types of Supporting Subsidiaries within the Sector.Familiarization of Standard Operating Procedures used within the Aviation Environment.Identify the Key Components within the Airport InfrastructureLearn the Differences in Equipment used within the Airport Ground Handling Activities.Identify Airport and Airside Lighting, Signage and Markings. The aviation industry encompasses almost all aspects of air travel and the activities of airport personnel help to facilitate it. The environment is impacted daily by technological challenges and brings rapid change internationally to stay ahead in its game. These pressures have significant effects on the way airports do business not only from a financial perspective but also from an operational standpoint. Airport operations demand the highest standards of safety, reliability, efficiency and comfort. Given a continuously growing demand for air traffic, a high concentration of movements and a limited place available to handle operations, it is required to implement optimized procedures and technologies and a close connection of all stakeholders. For instance: about 90,000 people employed and 140 airlines handled to ensure that up to 90 million passengers are being carried annually at Dubai International Airport in the United Arab Emirates. Individuals who work within the sector are required to know the roles airports play in the economy in order to discover the various customers and partners which gain profitable to the industry.The roles of each individual within the industry are essential to the business as is the set of principles that the sectors operate within. This course highlights the fundamentals of the operations in the airport environment in order to provide key knowledge concepts to the respective learner. This course is designed to help persons who are starting a career in airport operations positions or all other aviation personnel who want to get a broader introduction to airport operations.

Udemy
Unlock the secrets of sales operations: data accuracy, strategy development, forecasting, & performance management What you'll learn: Understand the fundamental role of sales operations within an organization and its significance in driving revenue and operational efficiency.Develop strategic sales plans and optimize sales processes to maximize productivity, streamline workflows, and enhance overall performance.Cultivate effective communication and collaboration strategies to align sales operations goals with team objectives, fostering a cohesive and high-performing saMaster essential skills such as data accuracy and management, forecasting techniques, analytical interpretation, and proficiency in relevant sales technology to Are you ready to unlock the secrets to mastering sales operations and propel your career to new heights? Welcome to "Foundations of Sales Operations" – your gateway to becoming a powerhouse in the world of sales strategy and efficiency. In this comprehensive course, you'll embark on a transformative journey through six immersive modules, each meticulously crafted to equip you with the essential skills and knowledge needed to excel in sales operations. In Module 1, we'll lay the groundwork by delving into the fundamental principles of sales operations. From understanding its pivotal role within organizations to exploring real-world case studies showcasing successful strategies, you'll gain invaluable insights into driving revenue and efficiency like never before. Moving forward to Module 2, we'll dive deeper into the core functions of sales operations. You'll learn how to develop robust sales plans and strategies, optimize sales processes for maximum productivity, and leverage cutting-edge technology to enhance operations. With real-life examples illuminating the path, you'll be ready to implement best practices with confidence. Module 3 focuses on the critical relationship between sales operations and the sales team. You'll discover effective collaboration techniques, align goals with team objectives, and master communication strategies to foster a productive dynamic. Navigate challenges with ease and cultivate a harmonious environment for unparalleled success. In Module 4, we'll hone in on the essential skills every sales operations professional needs to thrive. From mastering data accuracy and forecasting techniques to harnessing the power of analytics and visualization tools, you'll emerge with a toolkit primed for excellence. But we're just getting started. In Module 5, we'll delve into the art and science of forecasting. Learn how to build, validate, and interpret forecasting models with precision, empowering you to make data-driven decisions that propel your organization forward. Finally, in Module 6, we'll explore the latest innovations and industry-leading practices shaping the future of sales operations. Discover continuous improvement strategies, benchmarking techniques, and adaptability to market trends, ensuring you stay ahead of the curve in today's dynamic landscape. As we conclude this transformative journey, we'll recap key concepts covered throughout the course and provide guidance on further resources for your continued learning and development in sales operations. Don't miss out on this opportunity to elevate your career and become a driving force in sales operations. Enroll now and unlock your full potential! You'll Also Get:Udemy Certificate of Completion Ready for DownloadDon't Miss Out!Every second you wait is costing you valuable leads and sales.This course comes with a 30-day money-back guarantee - so there's no risk to getting started.Go ahead and hit the "take this course" butto

YouTube
Embark on a deep dive into the static analysis of Active Directory NTDS in this 44-minute conference talk from TROOPERS24 IT security conference. Join speakers Bastien Cacace and Florian Duthu as they unravel the complexities of the Active Directory database structure. Gain valuable insights into the inner workings of NTDS, exploring techniques for decrypting and analyzing this critical component of Windows domain environments. Learn about potential security implications and best practices for securing Active Directory infrastructures. Discover how static analysis can reveal hidden vulnerabilities and provide a better understanding of your organization's directory services. Whether you're a security professional, system administrator, or IT enthusiast, this talk offers a unique perspective on one of the most crucial elements of enterprise network security.

YouTube
Explore Chronicle Security Operations, an AI-powered platform for security teams, in this 17-minute video. Discover how Google's infrastructure and Mandiant's expertise combine to provide curated outcomes for proactive threat detection. Learn about the platform's key features, including the Alerts, Case, Playbook, and Overview tabs. Dive into a crypto mining case study and understand how to leverage historical EDR data and UDM search capabilities. Gain insights into detecting, investigating, and responding to cyber threats across hybrid environments with speed and precision.

Udemy
Operations Management Training Program (Course 7 of 8) What you'll learn: Identify the key differences between quality in manufacturing and service operations.Match quality performance objectives with indicators that are normally used as their measure.Identify quality management principles.Match phases of the transformation model with quality management activities that are typically carried out at each phase. The course on Management of Quality is part of the Operations Management Training Program which includes a number of eight sections also presented as individual courses for your convenience.Quality is an essential ingredient for any successful company. A company with quality products and services takes the time to get to know its customers and their expectations. When a company stops being committed to quality, it starts losing customers. In order to meet customers' expectations, a company must make quality a key concern at every stage of operations. From production to delivery and beyond, everyone in the company must be committed to the pursuit of quality.Quality is a complex term. It can refer to how well a product or service meets a company's own quality standards. Or it can refer to how well a company's product or service satisfies its customers. If its customers are unhappy, a company will find it difficult to survive in the marketplace. For a quality management strategy to succeed, a company's quality standards must be aligned with its customers' quality expectations.There are many different quality management strategies, and these can vary from organization to organization. Some quality management concepts and practices have been simplified in this course, for training purposes. Products and services are usually associated with manufacturing and service industries respectively. However, in this course, the term "product" is often used to represent "services" as well, to avoid redundancy.Quality is crucial to manufacturing and service industries. All organizations need to set quality performance metrics and measure the performance of their products, services, and processes on an ongoing basis. Quality management has evolved over many years. It's based on a number of key principles, which stress the vital role of suppliers, organization leaders, and customers in any quality initiative.When implementing a quality management strategy, companies can use many tools, including the transformation model and Lean Six Sigma. All these tools have the same ultimate goal – delivering quality to the customer.This course covers many quality management principles, techniques, and tools that can be applied in service or manufacturing organizations. All employees must understand and be committed to the organization's quality management strategy. By preparing for excellence, monitoring quality, and continuously improving, an organization can become a quality leader.That’s it! Now go ahead and push that “Take this course” button, and see you on the inside!

Udemy
Operations Management Training Program (Course 6 of 8) What you'll learn: Identify the main objectives of scheduling.Identify the key areas with which each level of scheduling is concerned.Identify the main challenges of scheduling of staff in a service environment.Calculate the minimum number of employees needed daily and weekly in a given service related scenarioMatch approaches to loading work centers with their characteristics.Sequence jobs using a variety of sequencing rules. The course on Operations Scheduling is part of the Operations Management Training Program which includes a number of eight sections also presented as individual courses for your convenience.Whether we realize it or not, we all conduct our everyday activities according to a schedule. Whether this schedule is formal or informal, highly organized or very casual, it's a schedule none the less. This course is concerned with operations schedules, which are by necessity always formal and organized. Operations scheduling is an integral part of operations management, as it assigns tasks to an organization's available resources, which can include facilities, personnel, machinery, and equipment. It also establishes the order for performing these tasks to meet production priorities and targets.Operations scheduling applies to a medium to short-term time frame and deals with tactical issues. It takes place once the long term strategic tasks such as demand forecasting and capacity planning have been completed. This course presents an overview of scheduling and explains the specific characteristics and challenges of scheduling in service-based organizations.The two major components of scheduling – loading and sequencing – will also be explained. Loading designates how jobs are assigned to resources, and sequencing provides the order in which they are carried out.That’s it! Now go ahead and push that “Take this course” button, and see you on the inside!

Udemy
AD DS Security with Lab: domain controllers, account security, audit authentication, managed service accounts, PSO What you'll learn: Securing domain controllersSecurity risks that can affect domain controllersModifying the security settings of domain controllersWhat are RODCs?Deploying an RODCConfiguring a password replication policyImplementing account securityPassword policiesAccount lockout policiesConfiguring a fine-grained password policyTools for creating PSOsImplementing audit authenticationAccount logon and logon eventsConfiguring managed service accounts This course is aimed to IT Pros and is supposed to give the viewer the information they need to know to get started with Active Directory (AD DS) and its key concepts. The goal is to provide coverage of ADDScomponents of advanced AD DS deployments, how to deploy a distributed AD DS environment and· Configure AD DS Security.The course is targeted to help learning Active Directory and do your job more efficiently.After completing this course, you will be able to:· Describe how to Secure domain controllers· Implementing account security.· Implementing audit authentication· Configuring managed service accounts In your organization’s information technology (IT) infrastructure, securing Active Directory Domain Services (AD DS) domain controllers is a critical task. Domain controllers provide access to many different resources, and they contain information about users and their passwords. If a single domain controller is compromised, any objects in the same Active Directory domain or in any trusted domain are at risk of being compromised, too.The Windows Server 2016 operating system provides features and apps that you can use to help secure your network against security threats. The operating system provides measures to secure domain controllers by minimizing their attack surface and determining their domain-controller placements. The operating system also determines the AD DS roles that are used for administration and design, and implements password security, in addition to auditing when attacks occur. You also can use domain controllers to deploy security measures to other clients and servers in your Windows-based infrastructure.AD DS administrators must understand the threats to domain controllers and the methods that they can use to secure AD DS and its domain controllers. ObjectivesAfter completing this module, you will be able to:· Secure domain controllers.· Implement account security.· Implement audit authentication.· Configure managed service accounts (MSAs).

YouTube
Explore the unintended risks associated with trusting Active Directory in this 48-minute conference talk from Derbycon 2018. Delve into security descriptors, Active Directory environments, and objects while examining the implications for workgroups and single hosts. Learn about weaponization techniques, persistence methods, and existing misconfigurations. Gain insights into Cobalt Strike and session enumeration as the speakers Lee Christensen, Will Schroeder, and Matt Nel share their expertise on this critical cybersecurity topic.
YouTube
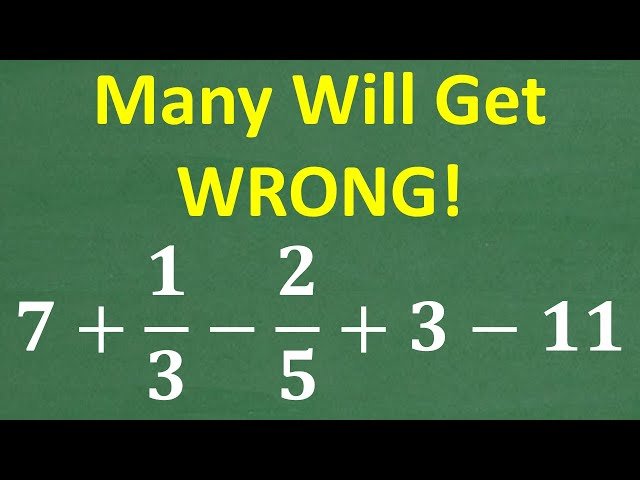
Watch this 10-minute tutorial that demonstrates how to solve a seemingly simple arithmetic problem involving mixed operations with whole numbers and fractions that commonly trips up many students. Work through the step-by-step process of calculating 7 + 1/3 - 2/5 + 3 - 11, learning proper order of operations and fraction manipulation techniques. Practice essential skills in addition, subtraction, working with fractions, and handling positive and negative numbers through this challenging example that highlights common mathematical pitfalls. Strengthen your foundational math abilities by understanding why this basic problem causes confusion and master the systematic approach needed to arrive at the correct answer.

YouTube
Explore the powerful capabilities of CrackMapExec for Active Directory penetration testing in this comprehensive conference talk from Derbycon 2016. Dive into the tool's libraries, witness live demonstrations, and learn advanced techniques for password spraying, spidering, and authentication. Discover how to perform admin actions, leverage payload modules, and execute Mimikatz. Gain insights into local and remote execution, database credential handling, and the use of various modules. Master the art of creating shells, implementing reverse HTTP handlers, and invoking shell modules. Enhance your cybersecurity skills with this in-depth exploration of CrackMapExec's features for owning Active Directory environments.

YouTube
Explore the evolution of Netflix's global Content Delivery Network (CDN) in this 41-minute conference talk from Strange Loop. Dive into the transition from commercial CDN providers to Netflix's in-house Open Connect system, and learn about the challenges and solutions in automating operations for this massive infrastructure. Discover how the Netflix team streamlined their automation processes, moving from large monolithic applications to a more scalable microservices architecture called the Open Connect Administration Platform. Gain insights into the history, future, pitfalls, and lessons learned throughout this automation journey, including topics such as physical server management, deployment locations, network connectivity, and the implementation of a platform-based approach with API gateways and GraphQL.

YouTube
Explore the evolving landscape of Special Operations Forces in this insightful 44-minute discussion featuring Richard Clarke, Commander of U.S. Special Operations Command, moderated by Michèle Flournoy, former Under Secretary of Defense for Policy. Gain valuable insights into the challenges, strategies, and future directions of these elite military units as they adapt to emerging global threats and technological advancements.
YouTube
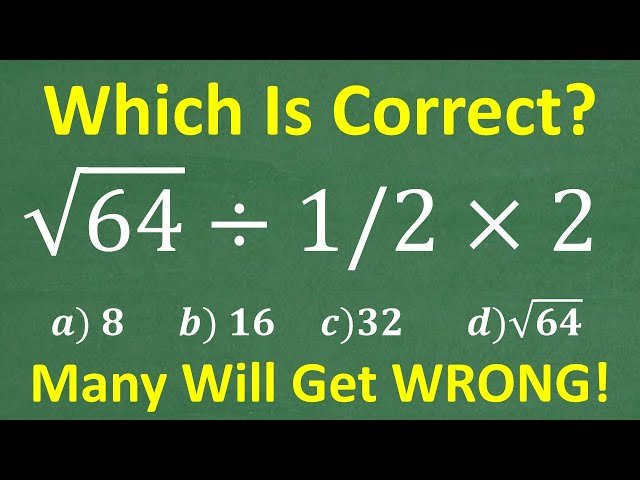
Learn to solve the viral math problem √64 ÷ ½ × 2 that stumps millions of people due to common misconceptions about order of operations and fraction division. Master the correct application of PEMDAS (order of operations) while discovering why dividing by ½ equals multiplying by 2 and understanding the crucial difference between "÷ ½" and "÷ 1 ÷ 2". Work through step-by-step solutions that reveal the most frequent mistakes students make when combining square roots, fraction operations, and multiplication. Develop essential algebraic skills applicable to middle school mathematics, Algebra 1, Algebra 2, and standardized test preparation including SAT, ACT, and GED exams. Practice with a challenging mathematical brain teaser that demonstrates fundamental concepts appearing throughout secondary mathematics education and serves as excellent preparation for homeschool math practice and test preparation scenarios.

