Courses
Discover thousands of courses from top institutions and platforms worldwide
Level
Course Type
Duration

FutureLearn
Some of the largest construction firms in the world have faced the prospect of multi-million fines for significant breaches of ethics and compliance recently – from bribery and collusion to modern slavery. Ethics is defined as a set of moral principles that govern a person’s behaviour or the conducting of an activity, but what does that mean for an individual or an organisation working in construction? Understand the role of ethics and compliance in the construction industry This free online course will help you to understand the concept of ethics, why they matter, and why being ethical goes deeper than just being compliant and legal. By the end of the five-week course, you will be able to: explain how ethics and compliance has a tangible impact on your professional role and personal values know why construction companies have policies and procedures, and how they relate to legal requirements and society; apply your company’s policy (or a sample policy) to a real-life ethical dilemma case study; identify conflicts of interest and determine the steps you need to take to minimise their risk; and ensure that your decisions are both ethical and compliant. Learn with construction ethics experts from the Chartered Institute of Building (CIOB) Construction Ethics and Compliance has been developed by The Chartered Institute of Building (CIOB) – the world’s largest and most influential professional body for construction management and leadership. The course will build on the CIOB’s experience of developing people in the science and practice of building, which it has been doing since 1834, as well as its recent work to create an International Standard for Ethics in the Built Environment. Are you a member of the CIOB? If you are a member preparing for professional review, the topics covered in this course will help you to recognise the things that you do that contribute to professional practice for Section 3 of your application. This course is suitable for everyone working in or studying construction. Whatever your level of experience, you will learn something new about ethics and compliance, and recognise your personal ethical standards. Whether you are site based, in a management, supervisory, procurement or technical role, or a teacher or trainer, this course will help you stay compliant, ethical and professional.

Udemy
Secure your business with Lecturio! What you'll learn: Develop the awareness of need and importance for compliance rulesLearn about compliance principles, money laundering, fraud prevention, securities trading, corruption prevention and data protection Compliance provides the right behavior to face a great variety of problematic situations during your everyday professional life. It applies not only for managers but also, and especially, for your employees. Remember that the price for an employee’s mistake is paid by the company – in form of legal repercussions, loss of image, or absences from work. Employees with no compliance training can end up being very expensive for your company. This is why compliance training starts with you, the manager. If you know the rules inside out, you can prevent breaches quicker and more effectively.Our compliance management training has a practical orientation and will raise your employees' awareness for the most important behavioral code – it's quick and easy!Is your company sufficiently protected against corruption and data gaps? How do you guarantee the security of information and data protection? Lecturio will familiarize you with the basics of compliance, such as fraud and corruption prevention. We provide helpful tips for your daily work and show you how to maintain good compliance management in your company.Learn about:- Compliance Principles - Money Laundering - Fraud Prevention - Securities Training - Corruption Prevention - Data Protection - Information Security - Competition LawWith the Lecturio compliance management video training you will learn about the important topics mentioned above independently and more efficiently than ever before, saving you a great deal of time and money!Protect your business with Lecturio's compliance course now!

Pluralsight
Technology continues to rapidly evolve, expand, and provide organizations unprecedented global reach. Understanding global privacy laws, import/export laws, and how various regulations can affect a business has never been more important. Businesses of all sizes can operate on a global scale. Privacy laws and data protection laws continue to evolve and become more restrictive. It's important for leaders to understand the changing landscape and what compliance means for their company. In this course, Law, Ethics, and Security Compliance Management, you will learn the foundations of global privacy law, import/export regulations, and how they can impact your organization. First, you’ll learn about the ever changing global privacy laws such as GDPR and CCPA. Next, you’ll learn about pertinent intellectual property concepts laws, along with key import/export laws. Finally, you’ll learn about the importance of taking an ethical approach to compliance management and how that not only strengthens your company’s security posture, but ensures the best chance for compliance with applicable laws and regulations. When you're finished with this course, you'll understanding global privacy laws, import/export laws, and how various regulations can affect a business.

Microsoft Learn
Module 1: In this module, you will learn why compliance management has become so important and be introduced to Microsoft’s solution for compliance management.At the end of this module, you should be able to:Describe why compliance management is important.List common compliance management challenges.Explain how Microsoft Compliance Manager helps you achieve compliance management goals.Module 2: In this module, you will learn about the shared responsibility model and important Compliance Manager concepts.At the end of this module, you should be able to:Describe the shared responsibility model.Explain key Compliance Manager concepts.Module 3: In this module, you will learn about the shared responsibility model and important Compliance Manager concepts.At the end of this module, you should be able to:Describe the key components of the Compliance Manager user experience.List key capabilities available in the various Compliance Manager features.

FutureLearn
Develop an understanding of unethical behaviour within treasury Financial institutions and corporate businesses highly value treasury professionals with up-to-date knowledge. This is because these professionals can help a business with their critical decision-making and overall success. On this four-week course, you’ll consider the importance of governance, ethics, compliance, and other forms of controls that treasury professionals encounter. You’ll also unpack the role of unethical behaviour and The Association of Corporate Treasurers’ (ACT) own ethical code, as this sets a minimum standard expected from all ACT members. By the end of this course, you’ll have the knowledge and confidence to deal with the challenges and opportunities that come from working in treasury. Unpack treasury control mechanisms To help minimise the risks associated with treasury, you’ll explore the control measures that can help save both money and reputation. You’ll delve into the internal control mechanisms to gain essential knowledge of how to handle the dealing limits and validations you may find in your work. Explore the treasury management system You’ll unpack the treasury management system and how you can use this software to automate tasks, save time, and become more organised. Next, you’ll explore conflicts of interest and develop the skills to deal with these issues when they arise. Understand the principles of corporate governance Finally, you’ll discover the principles of corporate governance to understand what makes good governance within treasury. Guided by experienced treasury experts, who work for the Association of Corporate Treasurers, you’ll finish the course with a solid understanding of governance, ethics, compliance, and audit for treasury professionals. This course is designed for anyone interested in governance, ethics, compliance, and other forms of controls that are typically encountered by treasury and finance professionals. No previous financial training or knowledge is necessary. If you are considering a career either with a corporate organisation, or within the financial organisations that they partner with such as banks and other financial institutions, this is a great way to kickstart your future development. N/A

LinkedIn Learning
Learn how to manage your manager. In this course, adapted from the podcast How to Be Awesome at Your Job, Mary Abbajay explains how to build a good relationship with your boss.

LinkedIn Learning
Learn how to create and manage apps with SCCM and prepare for Microsoft certification exam 70-703. See how to deploy apps using PowerShell scripts, and deploy App-V virtual apps.

LinkedIn Learning
Learn how to apply ethical standards and practices in the day-to-day execution of your leadership role.
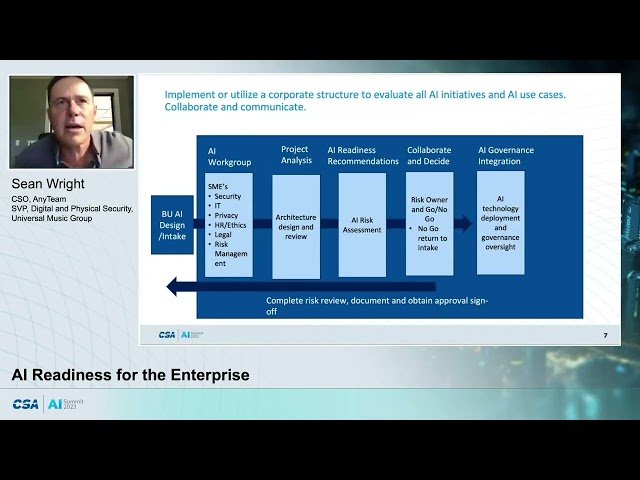
YouTube
Explore the essential aspects of AI readiness and learn the necessary steps for successful AI solution deployment in this 58-minute session presented by Sean Wright, Global SVP Digital and Physical Security at Universal Music Group. Delve into crucial considerations focusing on security, trust, ethics, and compliance. Gain insights into actionable steps and effective countermeasures required to securely and ethically deploy AI solutions while ensuring regulatory compliance. Discover strategies to navigate the complex landscape of AI implementation, equipping yourself with the knowledge to address potential challenges and maximize the benefits of AI technologies in your organization.

Microsoft Learn
This module introduces students to the various authentication methods used to protect identities.After this module, you should be able to: Describe Windows Hello for Business Describe Windows Hello deployment and management Describe Microsoft Entra ID Protection Describe and manage self-service password reset in Microsoft Entra ID Describe and manage multi-factor authentication This module describes how clients can be configured to access organizational resources using a virtual private network (VPN). Describe how you can access corporate resources Describe VPN types and configuration Describe Always On VPN Describe how to configure Always On VPN This module describes how to use compliance and conditional access policies to help protect access to organizational resources.After this module, you should be able to: Describe device compliance policy Deploy a device compliance policy Describe conditional access Create conditional access policies This module describes how to use Microsoft Endpoint Manager and Power BI to create compliance and custom reports.After this module, you should be able to: Generate inventory reports and Compliance reports using Microsoft Intune Report and monitor device compliance Create custom reports using the Intune Data Warehouse Use the Microsoft Graph API for building custom reports

Microsoft Learn
This module introduces students to the various authentication methods used to protect identities.After this module, you should be able to: Describe Windows Hello for Business Describe Windows Hello deployment and management Describe Microsoft Entra ID Protection Describe and manage self-service password reset in Microsoft Entra ID Describe and manage multi-factor authentication This module describes how clients can be configured to access organizational resources using a virtual private network (VPN).After this module, you should be able to: Describe how you can access corporate resources Describe VPN types and configuration Describe Always On VPN Describe how to configure Always On VPN This module describes how to use compliance and conditional access policies to help protect access to organizational resources.After this module, you should be able to: Describe device compliance policy Deploy a device compliance policy Describe conditional access Create conditional access policies This module describes how to use Microsoft Endpoint Manager and Power BI to create compliance and custom reports.After this module, you should be able to: Generate inventory reports and Compliance reports using Microsoft Intune Report and monitor device compliance Create custom reports using the Intune Data Warehouse Use the Microsoft Graph API for building custom reports

LinkedIn Learning
Explore essential Microsoft 365 features and controls that can help you manage your content lifecycle and comply with legal or regulatory standards.

Microsoft Learn
Module 1: Manage retention in emailBy the end of this module, you will be able to:Determine when and how to use retention tags in mailboxesAssign a retention policy to an email folderAdd optional retention policies to email messages and foldersRemove a retention policy from an email messageModule 2: Troubleshoot data governanceBy the end of this module, you will be able to:Explain how the retention age of elements is calculatedRepair retention policies that don't run as expectedUnderstand how to systematically troubleshoot when a retention policy appears to failConduct policy tests in test mode with policy tipsDescribe how to monitor DLP policies through message trackingModule 3: Explore sensitivity labelsBy the end of this module, you will be able to:Describe how sensitivity labels let you classify and protect your organization's dataIdentify the common reasons why organizations use sensitivity labelsExplain what a sensitivity label is and what they can do for an organizationConfigure a sensitivity label's scopeExplain why the order of sensitivity labels in your admin center is importantDescribe what label policies can doModule 4: Implement sensitivity labelsBy the end of this module, you will be able to:Describe the overall process to create, configure, and publish sensitivity labelsIdentify the administrative permissions that must be assigned to compliance team members to implement sensitivity labelsDevelop a data classification framework that provides the foundation for your sensitivity labelsCreate and configure sensitivity labelsPublish sensitivity labels by creating a label policyIdentify the differences between removing and deleting sensitivity labelsModule 5: Implement Windows Information ProtectionBy the end of this module, you will be able to:Describe Windows Information Protection and what it is used forPlan a deployment of Windows Information Protection policiesImplement Windows Information Protection policies in Windows desktop apps

Pluralsight
Windows client is installed and remote administrative access has been set up; what comes next? In this course, Windows Endpoint Administration: Manage Identity and Compliance, you will gain the ability to create and manage user and group accounts and configure systems with cloud-based policies to determine compliance and access to apps. First, you will explore how to secure Windows identities through the use of password management, tokens, and biometric authentication. Next, you will learn to manage users and groups in a domain environment, whether on-premises Active Directory or cloud-based Azure AD. Finally, you will see how to use Intune to build policies that evaluate device compliance with corporate configuration standards, and restrict access to applications based on compliance. When you are finished with this course, you will have the skills and knowledge to set up Windows 10 and 11 successfully for identity management, device compliance, and conditional access.

Microsoft Learn
This module introduces you to data classification in Microsoft 365, including how to create and train classifiers, view sensitive data using Content explorer and Activity explorer, and implement Document Fingerprinting.By the end of this module, you should be able to: Explain the benefits and pain points of creating a data classification framework. Identify how data classification of sensitive items is handled in Microsoft 365. Understand how Microsoft 365 uses trainable classifiers to protect sensitive data. Create and then retrain custom trainable classifiers. Analyze the results of your data classification efforts in Content explorer and Activity explorer. Implement Document Fingerprinting to protect sensitive information being sent through Exchange Online. This module examines how sensitivity labels from the Microsoft Information Protection solution let you classify and protect your organization's data, while making sure that user productivity and collaboration isn't hindered.By the end of this module, you should be able to: Describe how sensitivity labels let you classify and protect your organization's data Identify the common reasons why organizations use sensitivity labels Explain what a sensitivity label is and what they can do for an organization Configure a sensitivity label's scope Explain why the order of sensitivity labels in your admin center is important Describe what label policies can do This module examines the process for implementing sensitivity labels, including applying proper administrative permissions, determining a deployment strategy, creating, configuring, and publishing labels, and removing and deleting labels.By the end of this module, you should be able to: Create a deployment strategy for implementing sensitivity labels that satisfies your organization's requirements. Enable sensitivity labels in SharePoint Online and OneDrive so they can use encrypted files. Create and configure sensitivity labels. Publish sensitivity labels by creating a label policy. Identify the differences between removing and deleting sensitivity labels.
Coursera
Great leadership doesn't happen by chance—it happens by design. This course helps you create and evolve a personalized leadership checklist that keeps you focused on what matters most. You'll learn the core components of an effective checklist, from daily practices to strategic responsibilities, and how to structure them for clarity and action. Through practical tools, case examples, and hands-on activities, you'll build a Version 1 of your leadership checklist, test it against real challenges, and refine it as your role evolves.

Pluralsight
Learn how to enforce device configurations using compliance policies as you then deny access to corporate resources when machines go non-compliant. The conversation about device configuration over the last couple of courses has focused on just the configurations themselves. As performed, those configurations are more like preferences than any real policy. They configure machines, but users can adjust those configurations generally at will. In this thirteenth course out of sixteen, Microsoft Endpoint Manager: Compliance Policies with MECM and Intune, you'll learn enforcing configurations, declaring misconfigured machines as non-compliant, and then bringing consequences to those misconfigurations. First, you'll start by looking at compliance in MECM. Next, you'll configure some custom compliance policies in MECM including auto-remediation and see how they look from the user's perspective. Then, you'll shift over to Intune to explore the very different approach Intune uses to address compliance. You'll create and deploy Intune compliance policies to see their effect on user's machines. Finally, you'll connect compliance policies to conditional access policies and deny access to corporate resources when machines go non-compliant. By the end of this course, you'll have a better understanding of enforcing configurations to meet compliance in MECM and Intune.

LinkedIn Learning
Looking for a consistent and reliable way to install Windows applications? Learn about the Chocolatey package manager.

Microsoft Learn
Module 1: This module introduces you to data classification in Microsoft 365, including how to create and train classifiers, view sensitive data using Content explorer and Activity explorer, and implement Document Fingerprinting.By the end of this module, you should be able to: Explain the benefits and pain points of creating a data classification framework. Identify how data classification of sensitive items is handled in Microsoft 365. Understand how Microsoft 365 uses trainable classifiers to protect sensitive data. Create and then retrain custom trainable classifiers. Analyze the results of your data classification efforts in Content explorer and Activity explorer. Implement Document Fingerprinting to protect sensitive information being sent through Exchange Online. Module 2: This module examines how sensitivity labels from the Microsoft Information Protection solution let you classify and protect your organization's data, while making sure that user productivity and collaboration isn't hindered.By the end of this module, you should be able to: Describe how sensitivity labels let you classify and protect your organization's data Identify the common reasons why organizations use sensitivity labels Explain what a sensitivity label is and what they can do for an organization Configure a sensitivity label's scope Explain why the order of sensitivity labels in your admin center is important Describe what label policies can do Module 3: This module examines the process for implementing sensitivity labels, including applying proper administrative permissions, determining a deployment strategy, creating, configuring, and publishing labels, and removing and deleting labels.By the end of this module, you should be able to: Describe the overall process to create, configure, and publish sensitivity labels Identify the administrative permissions that must be assigned to compliance team members to implement sensitivity labels Develop a data classification framework that provides the foundation for your sensitivity labels Create and configure sensitivity labels Publish sensitivity labels by creating a label policy Identify the differences between removing and deleting sensitivity labels

YouTube
Explore the critical issues of data privacy, security, ethics, and compliance in this conference talk from PASS Data Community Summit. Delve into the challenges faced by data professionals in an era of rapid technological advancement, including machine learning, artificial intelligence, and big data processing. Learn about the ethical considerations surrounding data usage in business and the crucial role each data professional plays in upholding the highest standards. Discover tools and strategies to mitigate risks, maintain data integrity, and balance compliance requirements with emerging business opportunities. Gain valuable insights to protect your company's reputation and navigate the complex landscape of data ethics in today's data-driven world.

