Courses
Discover thousands of courses from top institutions and platforms worldwide
Level
Course Type
Duration

edX
This program provides learning opportunities focused on Microsoft security and compliance solutions. The Microsoft Defender course aims to equip individuals with the skills to utilize Defender for threat mitigation. It covers threat protection, detection, and response, focusing on configuration, management, understanding threat types, and implementing defensive strategies within a Microsoft environment. The goal is to enable users to proactively manage security incidents using Microsoft Defender. The Microsoft Sentinel course provides a comprehensive understanding of this cloud-native SIEM and SOAR solution. Learners will grasp key concepts, functionalities, and practical applications for security monitoring, threat detection, and incident response. The curriculum covers Sentinel fundamentals, deployment and configuration in Azure, data ingestion from various sources, threat detection and analysis using analytics, threat intelligence, and investigation tools. It also delves into automation and response using SOAR capabilities and playbooks, proactive threat hunting and investigation, and the use of Sentinel for compliance monitoring and reporting. The Microsoft Purview course concentrates on data protection and risk management. It includes implementing data loss prevention, managing information governance, and addressing compliance requirements. The content explores Purview's features for safeguarding sensitive data and maintaining regulatory compliance. Key areas include Data Loss Prevention (DLP) to identify and protect sensitive information, Information Governance for data management and retention, and Compliance Management to meet regulatory obligations and conduct audits.

Coursera
This course features Coursera Coach! A smarter way to learn with interactive, real-time conversations that help you test your knowledge, challenge assumptions, and deepen your understanding as you progress through the course. Become proficient in using Microsoft security tools to detect, investigate, and respond to cyber threats. You will gain hands-on experience with Microsoft Defender, Sentinel, and Microsoft 365 Defender to secure endpoints, identities, and cloud environments. Learn to configure security baselines, manage alerts, and automate threat response using these powerful security products. The course begins with an introduction to Microsoft 365 Defender, followed by comprehensive coverage of Defender for Office 365, Defender for Cloud Apps, Defender for Endpoint, and Defender for Identity. You will explore methods for threat hunting and analyze security data using advanced tools like Extended Detection and Response (XDR) and Microsoft Secure Score. The course progresses into Microsoft Defender for Cloud, helping you secure cloud infrastructure and multi-cloud environments. Next, you'll dive into Microsoft Sentinel, where you'll learn to configure resources, manage data connectors, and automate workflows for efficient incident response. The hands-on nature of the course ensures you gain practical skills in mitigating threats. This course is ideal for security professionals looking to gain in-depth knowledge of Microsoft security products. It is designed for those who have a foundational understanding of IT and cybersecurity concepts and are eager to advance their skills in threat detection and response.

Udemy
Pass SC-200 | Hands-on experience in your own free Azure environment What you'll learn: Configure settings in Microsoft Defender XDRManage assets and environmentsDesign and configure a Microsoft Sentinel workspaceIngest data sources in Microsoft SentinelConfigure protections in Microsoft Defender security technologiesConfigure detection in Microsoft Defender XDRConfigure detections in Microsoft SentinelRespond to alerts and incidents in Microsoft Defender XDRRespond to alerts and incidents identified by Microsoft Defender for EndpointEnrich investigations by using other Microsoft toolsManage incidents in Microsoft SentinelConfigure security orchestration, automation, and response (SOAR) in Microsoft SentinelHunt for threats by using KQLHunt for threats by using Microsoft SentinelAnalyze and interpret data by using workbooksImplement and use Copilot for Security SC-200: Microsoft Security Operations Analyst, is a meticulously structured Udemy course aimed at IT professionals seeking to pass the SC-200 exam. This course systematically walks you through the initial setup to advanced implementation with real-world applications.By passing SC-200: Microsoft Security Operations Analyst, you're gaining proficiency in the highly recognized Microsoft security operations ecosystem.The course is always aligned with Microsoft's latest study guide and exam objectives:Manage a security operations environment (20–25%)Configure protections and detections (15–20%)Manage incident response (25–30%)Manage security threats (15–20%)Manage a security operations environmentConfigure settings in Microsoft Defender XDRConfigure alert and vulnerability notification rulesConfigure Microsoft Defender for Endpoint advanced featuresConfigure endpoint rules settingsManage automated investigation and response capabilities in Microsoft Defender XDRConfigure automatic attack disruption in Microsoft Defender XDRManage assets and environmentsConfigure and manage device groups, permissions, and automation levels in Microsoft Defender for EndpointIdentify unmanaged devices in Microsoft Defender for EndpointDiscover unprotected resources by using Defender for CloudIdentify and remediate devices at risk by using Microsoft Defender Vulnerability ManagementMitigate risk by using Exposure Management in Microsoft Defender XDRDesign and configure a Microsoft Sentinel workspacePlan a Microsoft Sentinel workspaceConfigure Microsoft Sentinel rolesSpecify Azure RBAC roles for Microsoft Sentinel configurationDesign and configure Microsoft Sentinel data storage, including log types and log retentionIngest data sources in Microsoft SentinelIdentify data sources to be ingested for Microsoft SentinelImplement and use Content hub solutionsConfigure and use Microsoft connectors for Azure resources, including Azure Policy and diagnostic settingsPlan and configure Syslog and Common Event Format (CEF) event collectionsPlan and configure collection of Windows Security events by using data collection rules, including Windows Event Forwarding (WEF)Create custom log tables in the workspace to store ingested dataMonitor and optimize data ingestionConfigure protections and detectionsConfigure protections in Microsoft Defender security technologiesConfigure policies for Microsoft Defender for Cloud AppsConfigure policies for Microsoft Defender for Office 365Configure security policies for Microsoft Defender for Endpoints, including attack surface reduction (ASR) rulesConfigure cloud workload protections in Microsoft Defender for CloudConfigure detections in Microsoft Defender XDRConfigure and manage custom detection rulesManage alerts, including tuning, suppression, and correlationConfigure deception rules in Microsoft Defender XDRConfigure detections in Microsoft SentinelClassify and analyze data by using entitiesConfigure and manage analytics rulesQuery Microsoft Sentinel data by using ASIM parsersImplement behavioral analyticsManage incident responseRespond to alerts and incidents in the Microsoft Defender portalInvestigate and remediate threats by using Microsoft Defender for Office 365Investigate and remediate ransomware and business email compromise incidents identified by automatic attack disruptionInvestigate and remediate compromised entities identified by Microsoft Purview data loss prevention (DLP) policiesInvestigate and remediate threats identified by Microsoft Purview insider risk policiesInvestigate and remediate alerts and incidents identified by Microsoft Defender for Cloud workload protectionsInvestigate and remediate security risks identified by Microsoft Defender for Cloud AppsInvestigate and remediate compromised identities that are identified by Microsoft Entra IDInvestigate and remediate security alerts from Microsoft Defender for IdentityRespond to alerts and incidents identified by Microsoft Defender for EndpointInvestigate device timelinesPerform actions on the device, including live response and collecting investigation packagesPerform evidence and entity investigationInvestigate Microsoft 365 activitiesInvestigate threats by using the unified audit logInvestigate threats by using Content SearchInvestigate threats by using Microsoft Graph activity logsRespond to incidents in Microsoft SentinelInvestigate and remediate incidents in Microsoft SentinelCreate and configure automation rulesCreate and configure Microsoft Sentinel playbooksRun playbooks on on-premises resourcesImplement and use Copilot for SecurityCreate and use promptbooksManage sources for Copilot for Security, including plugins and filesIntegrate Copilot for Security by implementing connectorsManage permissions and roles in Copilot for SecurityMonitor Copilot for Security capacity and costIdentify threats and risks by using Copilot for SecurityInvestigate incidents by using Copilot for SecurityManage security threatsHunt for threats by using Microsoft Defender XDRIdentify threats by using Kusto Query Language (KQL)Interpret threat analytics in the Microsoft Defender portalCreate custom hunting queries by using KQLHunt for threats by using Microsoft SentinelAnalyze attack vector coverage by using the MITRE ATT&CK matrixManage and use threat indicatorsCreate and manage huntsCreate and monitor hunting queriesUse hunting bookmarks for data investigationsRetrieve and manage archived log dataCreate and manage search jobsCreate and configure Microsoft Sentinel workbooksActivate and customize workbook templatesCreate custom workbooks that include KQLConfigure visualizations

Udemy
Unlocking Financial Success: Mastering Stocks, Equities, and Mutual Funds What you'll learn: Stock Market Fundamentals: Gain a comprehensive understanding of how the stock market operates, including primary and secondary markets & trading hoursEffective Buying and Selling: Learn the intricacies of buying and selling stocks efficiently, from executing trades to managing your investments effectively.Investment Goals and Strategies: Develop a strategic approach to stock investing aligned with your personal financial goals and risk tolerance.Brokerage Account Management: Discover the key elements of managing a brokerage account, including account types, fees, and account maintenance.Differentiating Investment Approaches: Differentiate between investment and trading strategies, and understand the distinctions between stocks, ETFs, and mutualAdvanced Investment Instruments: Explore advanced investment instruments such as options, futures, and their role in a diversified portfolio.Corporate Actions Impact: Understand how corporate actions, such as dividends, stock splits, and preferred stock issuance, impact your investment portfolio.Analyzing Company Financials: Develop the skills to analyze a company's financial position, evaluate stock sectors, and make informed investment decisions.Technical Analysis Mastery: Dive into technical analysis techniques to identify trends, patterns, and potential investment opportunities in stock trading.Advanced Stock Concepts: Explore advanced stock concepts like convertible preferred stock, cumulative preferred stock, and earnings per share (EPS).Financial Metric Proficiency: Master financial metrics including price-to-earnings (P/E) ratio, beta, and book value per share (BVPS)Valuation Models: Gain expertise in valuation models such as the Dividend Discount Model (DDM) and learn investment strategies like dollar-cost averaging.Dividend Reinvestment: Discover the benefits of dividend reinvestment plans (DRIP) and their impact on long-term investment growth.Leveraging Margin and Short Selling: Explore advanced strategies like buying on margin and short selling to maximize investment opportunities.Global Investment Strategies: Understand international investing using tools like the Capital Asset Pricing Model (CAPM) for diversified portfolios.Dividend Income Estimation: Calculate crucial financial metrics including dividend yield, forward P/E ratio, and payout ratio.Portfolio Optimization: Learn to optimize a diversified stock portfolio effectively by applying advanced techniques.Asset Allocation Strategies: Explore asset allocation strategies for risk management and investment diversification.Market Analysis: Apply technical and fundamental analysis to make informed investment decisions in varying market conditions.Risk Management: Develop strategies to manage investment risks, including strategies for income, value, and growth stocks.Investment Psychology: Understand the psychological aspects of investing and learn to make rational decisions amid market fluctuations.Investment Regulations: Familiarize yourself with relevant investment regulations and ethical considerations in stock investing. Welcome to this comprehensive course designed to empower you with the knowledge and skills required to navigate the intricate world of investing in stocks, equities, and mutual funds.Understanding the Stock Market:Our journey begins with a deep dive into the stock market. You'll gain a profound understanding of both primary and secondary markets, learning how stocks are bought and sold. Explore the fascinating inner workings of various stock exchanges, from their trading hours to their unique characteristics. Gain insight into the psychology of market participants and how market sentiment influences stock prices.Mastering Stock Investing:In this section, we demystify stock investing. Discover what it means to own a share in a company and learn the intricacies of trading stocks. We'll guide you through the process of selling your stock holdings and provide valuable insights into different stock categories, including income, value, and growth stocks. You'll also become well-versed in handling commissions and fees effectively.Exploring Investment Vehicles:Dive into the diverse array of investment options available. Navigate the world of individual stocks, exchange-traded funds (ETFs), and mutual funds. By understanding the unique features of each choice, you'll be equipped to make investment decisions aligned with your financial objectives. Explore how ETFs and mutual funds are structured, how they are traded, and their advantages and disadvantages.Mastering Stock Fundamentals:Develop the skills to analyze a company's financial health confidently. We'll explore both quantitative and qualitative methods for assessing a company's performance. Gain insights into stock sectors and learn how to interpret financial statements with precision. Learn how to conduct comprehensive fundamental analysis, including evaluating a company's income statement, balance sheet, and cash flow statement.Analyzing Stocks Like a Pro:Equip yourself with the tools used by seasoned investors. Unlock the potential of technical analysis and learn how to apply it to your investment strategies. Delve into the implications of corporate actions, such as stock splits and reverse stock splits, to make informed decisions. Learn how to use stock charts, technical indicators, and chart patterns to identify potential investment opportunities.Understanding Preferred Stocks:Venture into the world of preferred stocks. Discover various types, including cumulative, callable, and convertible preferred stocks. Gain insights into perpetual and adjustable-rate preferred stocks, broadening your investment horizons. Explore how preferred stocks differ from common stocks and bonds, and how to evaluate their suitability for your portfolio.Performance Evaluation and Risk Management:Learn to navigate stock valuation complexities. Master the art of calculating key metrics like Price-to-Earnings (P/E) ratios, Price/Earnings-to-Growth (PEG) ratios, and Beta. Dive deep into the Dividend Discount Model (DDM) to assess stock values accurately. Understand how to assess the risk associated with individual stocks and build a diversified portfolio to manage risk effectively.Strategies for Savvy Investing:Explore essential investment strategies like dollar-cost averaging and value averaging. Dive into Dividend Reinvestment Plans (DRIPs) and gain an in-depth understanding of buying on margin and short selling to make well-informed investment decisions. Learn about different investment styles, including value investing, growth investing, and income investing, and how to apply them to your portfolio.Global Investment Perspectives:Expand your investment horizons globally. Dive into the International Capital Asset Pricing Model (CAPM) and discover how to estimate dividend income effectively in a global context. Understand the factors that influence international stock markets and how to assess opportunities and risks when investing internationally.Calculating Returns with Precision:Unlock the secrets of investment returns. Learn how to calculate dividends, earnings per share (EPS), and the price-earnings ratio (P/E ratio) with precision. Explore various methods for projecting future returns with confidence. Understand the concept of total return and how it can impact your investment decisions.Join Us on a Journey to Financial Prosperity:This comprehensive course caters to both beginners and those with prior investment knowledge. Whether you aspire to build wealth, seek to grasp the intricacies of financial markets, or enhance your investment skills, this course is your gateway to success.Embark on a Path to Investment Expertise:Get ready to embark on a path toward financial prosperity and investment expertise. Enroll now and take the first step toward securing your financial future. Don't miss this opportunity to master the art of investing in stocks and mutual funds and gain the financial knowledge you need for a successful future. Start your journey today!

Udemy
Learn all about Microsoft security services, Microsoft Sentinel, KQL, Microsoft 365 Defender suite and get certified What you'll learn: Explain how Microsoft Defender for Endpoint can remediate risks in your environmentCreate a Microsoft Defender for Endpoint environmentConfigure Attack Surface Reduction rules on Windows devicesConfigure alert settings in Microsoft Defender for EndpointConduct advanced hunting in Microsoft 365 DefenderManage incidents in Microsoft 365 DefenderInvestigate DLP alerts in Microsoft Defender for Cloud AppsExplain the types of actions you can take on an insider risk management caseConfigure Microsoft Defender for CloudRemediate alerts in Microsoft Defender for CloudConstruct Kusto Query Language (KQL) statementsExtract data from unstructured string fields using KQLManage a Microsoft Sentinel workspaceUse KQL to access the watchlist in Microsoft SentinelManage threat indicators in Microsoft SentinelConfigure different data sources in Microsoft Sentinel This course is a complete preparation for the SC-200 exam. ( Including hands-on Labs)The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders.Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Don't be left behind. Be ahead of the curve by getting certified as a Microsoft Security Operations Analyst, and be ready for the opportunity to advance your career in Cybersecurity.All video lectures will cover all SC-200 exam topics and include hands on demonstrations on each topic.The course has been structured to follow the exact official Microsoft training plan. So if you want to pass your exam on your first attempt hit the enroll button now and you will get: · Video lectures on each topic of the exam with demos that fully prepare you for your exam as well as ensuring you can administer all Microsoft security services and tools like a Pro · Review questions at the end of each section (quizz) to test your knowledge on the topics learned in the section · LABS at the end of each section. The labs follow the official Microsoft training labs and they are designed so you can practice yourself at your own pace when you aren't watching the videos. You will have step-by-step instructions available to complete each lab and instructions to prepare your lab environment and deploy the necesarry resources for the labs. · Interactive pre-recorded demonstrations on some of the topics that cannot be covered in the lab environment · Links to official Microsoft resources/blogs/videos for further documentation available for each lesson on each topic This course curriculum follows the Microsoft's SC-200 exam study areas: · Mitigate threats using Microsoft 365 Defender (25-30%) · Mitigate threats using Microsoft Defender for Cloud (25-30%) · Mitigate threats using Microsoft Sentinel (40-45%) Microsoft, Windows, Microsoft 365 and Microsoft Azure are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries. This course is not certified, accredited, affiliated with, nor endorsed by Microsoft Corporation.

CourseHorse
Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Audience Profile The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Job role: Security Engineer Preparation for exam: SC-200 Skills gained • Explain how Microsoft Defender for Endpoint can remediate risks in your environment • Administer a Microsoft Defender for Endpoint environment • Configure Attack Surface Reduction rules on Windows devices • Perform actions on a device using Microsoft Defender for Endpoint • Investigate domains and IP addresses in Microsoft Defender for Endpoint • Investigate user accounts in Microsoft Defender for Endpoint • Configure alert settings in Microsoft 365 Defender • Explain how the threat landscape is evolving • Conduct advanced hunting in Microsoft 365 Defender • Manage incidents in Microsoft 365 Defender • Explain how Microsoft Defender for Identity can remediate risks in your environment • Investigate DLP alerts in Microsoft Defender for Cloud Apps • Explain the types of actions you can take on an insider risk management case • Configure auto-provisioning in Microsoft Defender for Cloud Apps • Remediate alerts in Microsoft Defender for Cloud Apps • Construct KQL statements • Filter searches based on event time, severity, domain, and other relevant data using KQL • Extract data from unstructured string fields using KQL • Manage a Microsoft Sentinel workspace • Use KQL to access the watchlist in Microsoft Sentinel • Manage threat indicators in Microsoft Sentinel • Explain the Common Event Format and Syslog connector differences in Microsoft Sentinel • Connect Azure Windows Virtual Machines to Microsoft Sentinel • Configure Log Analytics agent to collect Sysmon events • Create new analytics rules and queries using the analytics rule wizard • Create a playbook to automate an incident response • Use queries to hunt for threats • Observe threats over time with livestream Prerequisites • Basic understanding of Microsoft 365 • Fundamental understanding of Microsoft security, compliance, and identity products • Intermediate understanding of Windows 10 • Familiarity with Azure services, specifically Azure SQL Database and Azure Storage • Familiarity with Azure virtual machines and virtual networking • Basic understanding of scripting concepts.Your course includes: COURSE OUTLINE Module 1: Mitigate threats using Microsoft 365 Defender Analyze threat data across domains and rapidly remediate threats with built-in orchestration and automation in Microsoft 365 Defender. Learn about cybersecurity threats and how the new threat protection tools from Microsoft protect your organization’s users, devices, and data. Use the advanced detection and remediation of identity-based threats to protect your Azure Active Directory identities and applications from compromise. Lessons • Introduction to threat protection with Microsoft 365 • Mitigate incidents using Microsoft 365 Defender • Remediate risks with Microsoft Defender for Office 365 • Microsoft Defender for Identity • Protect your identities with Azure AD Identity Protection • Microsoft Defender for Cloud Apps • Respond to data loss prevention alerts using Microsoft 365 • Manage insider risk in Microsoft 365 Module 2: Mitigate threats using Microsoft Defender for Endpoint Implement the Microsoft Defender for Endpoint platform to detect, investigate, and respond to advanced threats. Learn how Microsoft Defender for Endpoint can help your organization stay secure. Learn how to deploy the Microsoft Defender for Endpoint environment, including onboarding devices and configuring security. Learn how to investigate incidents and alerts using Microsoft Defender for Endpoint. Perform advanced hunting and consult with threat experts. You will also learn how to configure automation in Microsoft Defender for Endpoint by managing environmental settings. Lastly, you will learn about your environment's weaknesses by using Threat and Vulnerability Management in Microsoft Defender for Endpoint. Lessons • Protect against threats with Microsoft Defender for Endpoint • Deploy the Microsoft Defender for Endpoint environment • Implement Windows security enhancements • Perform device investigations • Perform actions on a device • Perform evidence and entities investigations • Configure and manage automation • Configure for alerts and detections • Utilize Threat and Vulnerability Management Module 3: Mitigate threats using Microsoft Defender for Cloud Use Microsoft Defender for Cloud, for Azure, hybrid cloud, and on-premises workload protection and security. Learn the purpose of Microsoft Defender for Cloud and how to enable it. You will also learn about the protections and detections provided by Microsoft Defender for Cloud for each cloud workload. Learn how you can add Microsoft Defender for Cloud capabilities to your hybrid environment. Lessons • Plan for cloud workload protections using Microsoft Defender for Cloud • Workload protections in Microsoft Defender for Cloud • Connect Azure assets to Microsoft Defender for Cloud • Connect non-Azure resources to Microsoft Defender for Cloud • Remediate security alerts using Microsoft Defender for Cloud Module 4: Create queries for Microsoft Sentinel using Kusto Query Language (KQL) Write Kusto Query Language (KQL) statements to query log data to perform detections, analysis, and reporting in Microsoft Sentinel. This module will focus on the most used operators. The example KQL statements will showcase security related table queries. KQL is the query language used to perform analysis on data to create analytics, workbooks, and perform hunting in Microsoft Sentinel. Learn how basic KQL statement structure provides the foundation to build more complex statements. Learn how to summarize and visualize data with a KQL statement provides the foundation to build detections in Microsoft Sentinel. Learn how to use the Kusto Query Language (KQL) to manipulate string data ingested from log sources. Lessons • Construct KQL statements for Microsoft Sentinel • Analyze query results using KQL • Build multi-table statements using KQL • Work with string data using KQL statements Module 5: Configure your Microsoft Sentinel environment Get started with Microsoft Sentinel by properly configuring the Microsoft Sentinel workspace. Traditional security information and event management (SIEM) systems typically take a long time to set up and configure. They're also not necessarily designed with cloud workloads in mind. Microsoft Sentinel enables you to start getting valuable security insights from your cloud and on-premises data quickly. This module helps you get started. Learn about the architecture of Microsoft Sentinel workspaces to ensure you configure your system to meet your organization's security operations requirements. As a Security Operations Analyst, you must understand the tables, fields, and data ingested in your workspace. Learn how to query the most used data tables in Microsoft Sentinel. Lessons • Introduction to Microsoft Sentinel • Create and manage Microsoft Sentinel workspaces • Query logs in Microsoft Sentinel • Use watchlists in Microsoft Sentinel • Utilize threat intelligence in Microsoft Sentinel Module 6: Connect logs to Microsoft Sentinel Connect data at cloud scale across all users, devices, applications, and infrastructure, both on-premises and in multiple clouds to Microsoft Sentinel. The primary approach to connect log data is using the Microsoft Sentinel provided data connectors. This module provides an overview of the available data connectors. You will get to learn about the configuration options and data provided by Microsoft Sentinel connectors for Microsoft 365 Defender. Lessons • Connect data to Microsoft Sentinel using data connectors • Connect Microsoft services to Microsoft Sentinel • Connect Microsoft 365 Defender to Microsoft Sentinel • Connect Windows hosts to Microsoft Sentinel • Connect Common Event Format logs to Microsoft Sentinel • Connect syslog data sources to Microsoft Sentinel • Connect threat indicators to Microsoft Sentinel Module 7: Create detections and perform investigations using Microsoft Sentinel Detect previously uncovered threats and rapidly remediate threats with built-in orchestration and automation in Microsoft Sentinel. You will learn how to create Microsoft Sentinel playbooks to respond to security threats. You'll investigate Microsoft Sentinel incident management, learn about Microsoft Sentinel events and entities, and discover ways to resolve incidents. You will also learn how to query, visualize, and monitor data in Microsoft Sentinel. Lessons • Threat detection with Microsoft Sentinel analytics • Security incident management in Microsoft Sentinel • Threat response with Microsoft Sentinel playbooks • User and entity behavior analytics in Microsoft Sentinel • Query, visualize, and monitor data in Microsoft Sentinel Module 8: Perform threat hunting in Microsoft Sentinel In this module, you'll learn to proactively identify threat behaviors by using Microsoft Sentinel queries. You'll also learn to use bookmarks and livestream to hunt threats. You will also learn how to use notebooks in Microsoft Sentinel for advanced hunting. Lessons • Threat hunting concepts in Microsoft Sentinel • Threat hunting with Microsoft Sentinel • Hunt for threats using notebooks in Microsoft Sentinel

Udemy
Become a Microsoft SOC engineer Today!! Learn through lab excercises and practical demonstrations What you'll learn: Define the capabilities of Microsoft Defender for Endpoint.Understand how to hunt threats within your network.Explain how Microsoft Defender for Endpoint can remediate risks in your environment.Create a Microsoft Defender for Endpoint environmentOnboard devices to be monitored by Microsoft Defender for EndpointConfigure Microsoft Defender for Endpoint environment settingsInvestigate incidents in Microsoft Defender for EndpointInvestigate alerts in Microsoft Defender for EndpointPerform advanced hunting in Microsoft Defender for EndpointConfigure alert settings in Microsoft Defender for EndpointConstruct KQL statementsManage indicators in Microsoft Defender for EndpointDescribe Threat and Vulnerability Management in Microsoft Defender for EndpointIdentify vulnerabilities on your devices with Microsoft Defender for EndpointTrack emerging threats in Microsoft Defender for Endpoint There is no short cut to learning Azure security. This course teaches you how to learn it the right way with tons of labs excercises and the right volume of labs . The Microsoft Security Operations Analyst works with organizational stakeholders to secure the organization's information technology systems. Their mission is to reduce corporate risk by quickly resolving active attacks in the environment, advising on threat protection practices, and reporting policy violations to the proper stakeholders.Threat management, monitoring, and response using a variety of security technologies across their environment are among their responsibilities. Using Microsoft Azure Sentinel, Azure Defender, Microsoft 365 Defender, and third-party security tools, the position primarily investigates, responds to, and hunts for threats. The security operations analyst is a key stakeholder in the configuration and implementation of these technologies since they consume the operational output of these solutions.The following topics needs to be completed in order to achieve SC - 200 Certification. Module 1 Mitigate threats using Microsoft 365 Defender Module 2 Mitigate threats using Microsoft Defender for Endpoint Module 3 Mitigate threats using Azure Defender Module 4 Create queries for Azure Sentinel using Kusto Query Language Module 5 Microsoft Sentinel Environment - Configuration Module 6 Microsoft Sentinel Environment - Connecting Logs Module 7 Microsoft Sentinel Environment - Incidents,Threat Response , UEBA and Monitoring Module 8 Module 8 Perform Threat Hunting with Microsoft SentinelYou will learn and prepare to Implement the Microsoft Defender for Endpoint platform to detect, investigate, & respond to advanced threats. This learning path aligns with exam SC-200: Microsoft Security Operations Analyst Exam. Reviews from Participants - In the beginning I was a little intimidated by the immensity of Microsoft security environment, but getting along with the course it all clicked in my head. The concepts are presented at a very good pace and I like that the information is on point. Segmenting the videos in small chunks is also beneficial for time management. I really appreciate and recommend this course! - Adrian CarbuneGreat course. I learned a lot about Defender and Sentinel. I especially liked the module on KQL. IMO, it's the best tutorial on Kusto that I've found on the web. If Anand were to create a course that went in-depth on KQL I would certainly purchase it.-Bill JonesAnand has structured the course well, so that anyone, irrespective of their experience in Security, would be able to follow with ease. The course aligns very well with the Certification track. I strongly recommend this course to anyone who is interested in understanding Security.-Moses Mam truley satisfied with this course. Anand nails the security features of M 365 defender suite. The graphics , narration and worlkflows are commendable. Just labs, labs and labs . Its all about getting straight to the point. Great Job!!!-Gaurav Great course, congratulations to teacher! Help me a lot to gain very knowledge about Defender and Sentinel. I appreciate it!!!-Alexandre Gammaro It was one of the The best course .Your are an amazing Instructor.-NavidThis course is Awsome! One of the best I've ever made over here in Udemy platform.-Mauricio Kobayashi

Udemy
SC-200: Unlock the World of Security Operations Analyst, Skills & Success for SOC Analyst, Microsoft SC-200 Exam Prep. What you'll learn: Gain a clear understanding of the course structure, objectives, and the significance of the SC-200 certification.Develop insights into threats, vulnerabilities, and risks that organizations face.Dive into the Microsoft 365 Defender suite and its components.Explore the role of a Security Operations Analyst and the key responsibilities associated with the position.Explore the world of Security Information and Event Management (SIEM) tools.Grasp the fundamentals of Azure Defender and its role in protecting Azure resources.Acquire the fundamentals of incident response, from identification to resolution.Learn techniques for proactive threat hunting.Security Awareness and TrainingGain insights into different compliance frameworks.Understand the importance of Security Orchestration, Automation, and Response (SOAR).Career Paths and OpportunitiesGet an overview of the SC-200 exam and effective study strategies.and much more Welcome to the comprehensive and transformative journey of my Microsoft SC-200 Security Operations Analyst Certification Training CourseIn this meticulously crafted program, we delve deep into the intricate world of security operations, equipping you with the skills, knowledge, and insights needed to excel in this dynamic fieldMicrosoft security operations analysts reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. They perform triage, incident response, vulnerability management, threat hunting, and cyber threat intelligence analysisMicrosoft security operations analysts monitor, identify, investigate, and respond to threats in multi-cloud environments by using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security solutions. Microsoft security operations analysts collaborate with business stakeholders, architects, identity administrators, Azure administrators, and endpoint administrators to secure IT systems for the organizationFrom the fundamental principles of threat protection to advanced incident response strategies, we cover it all. Navigate through the realms of Microsoft 365 Defender and Azure Defender, understanding how to safeguard digital landscapes with finesse. Grasp the art of building a robust security culture and compliance framework, ensuring data protection and privacy regulations are metOur hands-on lectures, thought-provoking discussions, and immersive practical exercises enable you to grasp each concept with precision. You'll gain proficiency in utilizing Security Information and Event Management (SIEM) tools, Security Orchestration, Automation, and Response (SOAR) systems, and even sharpen your threat hunting skillsBut this course goes beyond mere certification preparation – it's a pathway to professional growth. Uncover diverse career opportunities in cybersecurity, discover the secrets to building a successful security operations career, and understand the power of continuous learning and developmentJoin us on this enriching voyage, where you'll emerge not only as a certified Microsoft SC-200 professional but also as a guardian of digital resilience, ready to defend against evolving threats and contribute effectively to the world of security operationsI hope to see you in this "Microsoft SC-200 Security Operations Analyst Essentials" journeyLet's get startedThank youIMPORTANT before enrolling:This course is not intended to replace studying any official vendor material for certification exams, is not endorsed by the certification vendor, and you will not be getting the official certification study material or a voucher as a part of thiscourse

Udemy
Jump-start your cybersecurity career from the gateway to success: A SOC Analyst (2025) What you'll learn: Learn what it takes to begin your career in cybersecurity from the easiest point of entry.Learn about how the pandemic impacted the demand for cybersecurity.Learn why the Security Operations Center (SOC) Analyst position is in high demand and the challenges hiring managers face.Learn strategies for applying for an interview in cybersecurity as a Security Operations Center (SOC) Analyst.Learn the common questions typically asked during a Security Operations Center (SOC) Analyst interview.Learn the prerequisite skills needed for a Security Operations Center (SOC) Analyst including network and cybersecurity fundamentals.Learn common commercial tools that are used by Security Operations Center (SOC) Analysts frequently in Enterprise environments.Learn and familiarize yourself with common terms and definitions used on a day-to-day basis as a Security Operations Center (SOC) Analyst.Learn fast facts about cloud technologies and cybersecurity in the cloud to prepare you for the future.Learn strategies on how to stay ahead of the curve with Security Operations Center (SOC) Automation.Learn how to conduct a structured security analysis using The SOC Analyst MethodPractice cloud engineering and SOC skills with hands-on projectsRead inspiring SOC stories from Analysts just like youPractice cryptography and networking in a unique course assignment Join 20,000+ students in this top hands-on Cybersecurity SOC course based on the best-selling book! The frontlines of cybersecurity operations include many unfilled jobs and exciting career opportunities.A transition to a security operations center (SOC) analyst position could be the start of a new path for you. Learn to actively analyze threats, protect your enterprise from harm, and kick-start your road to cybersecurity success with this one-of-a-kind course. Author Tyler E. Wall carefully and expertly share real-world insights and practical tips in SOCAnalyst NOW 2nd edition! The lessons revealed equip you for interview preparation, tackling day one on the job, and setting long-term development goals.This course highlights personal stories from six SOC professionals at various career levels with keen advice that is immediately applicable to your own journey. The gems of knowledge shared in this course provide you with a notable advantage for entering this dynamic field of work. The recent surplus in demand for SOC analysts makes SOCAnalyst NOW! a must-have for aspiring tech professionals and long-time veterans alike. Recent industry developments such as using the cloud and security automation are broken down in concise, understandable ways, to name a few. The rapidly changing world of cybersecurity requires innovation and fresh eyes, and this course is your roadmap to success. New to this edition:This revised edition includes three entirely new lectures: Roadmap to Cybersecurity Success, The SOC Analyst Method, and ChatGPT for SOC Analysts. The course was completely re-recorded using our latest technology, graphics, and content. What You Will LearnUnderstand the demand for SOC analystsKnow how to find a SOC analyst job fastBe aware of the people you will interact with as a SOC analystBe clear on the prerequisite skills needed to be a SOC analyst and what to studyBe familiar with the day-to-day life of a SOC analyst, including the tools and language usedDiscover the rapidly emerging areas of a SOC analyst job: the cloud and security automationExplore the career paths of a SOC analystDiscover background-specific tips for your roadmap to cybersecurity successKnow how to analyze a security eventKnow how to apply ChatGPT as a SOC analyst Who This Course Is ForAnyone interested in starting a career in cybersecurity: recent graduates, IT professionals transitioning into security, veterans, and those who are self-taught. Whats Included High Quality Lectures Practice Quizzes and TestThree Hands-On AssignmentsChallenging Course Capstone ProjectInspiring SOCAnalyst StoriesCertificate No Risk: Preview videos from the course now for FREE, and enjoy a 30-day money-back guarantee when you enroll - zero risk, unlimited payoff! And, we've made this course easy to afford so anyone can get started now! *Based on the popular bookJump-start Your SOC Analyst Career 2nd Edition - Available on Amazon.

Udemy
SC-200: Navigate the World of Security Operations Analyst, Skills & Success for SOC Analyst, Microsoft SC-200 Exam Prep. What you'll learn: Gain a clear understanding of the course structure, objectives, and the significance of the SC-200 certification.Explore the role of a Security Operations Analyst and the key responsibilities associated with the position.Develop insights into threats, vulnerabilities, and risks that organizations face.Dive into the Microsoft 365 Defender suite and its components.Grasp the fundamentals of Azure Defender and its role in protecting Azure resources.Acquire the fundamentals of incident response, from identification to resolution.Explore the world of Security Information and Event Management (SIEM) tools.Understand the importance of Security Orchestration, Automation, and Response (SOAR).Learn techniques for proactive threat hunting.Gain insights into different compliance frameworks.Security Awareness and TrainingCareer Paths and OpportunitiesGet an overview of the SC-200 exam and effective study strategies.and much more Welcome to the comprehensive and transformative journey of our Microsoft SC-200 Security Operations Analyst Certification Course. In this meticulously crafted program, we delve deep into the intricate world of security operations, equipping you with the skills, knowledge, and insights needed to excel in this dynamic field.Microsoft security operations analysts reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. They perform triage, incident response, vulnerability management, threat hunting, and cyber threat intelligence analysis.Microsoft security operations analysts monitor, identify, investigate, and respond to threats in multicloud environments by using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security solutions. Microsoft security operations analysts collaborate with business stakeholders, architects, identity administrators, Azure administrators, and endpoint administrators to secure IT systems for the organization.From the fundamental principles of threat protection to advanced incident response strategies, we cover it all. Navigate through the realms of Microsoft 365 Defender and Azure Defender, understanding how to safeguard digital landscapes with finesse. Grasp the art of building a robust security culture and compliance framework, ensuring data protection and privacy regulations are met.Our hands-on lectures, thought-provoking discussions, and immersive practical exercises enable you to grasp each concept with precision. You'll gain proficiency in utilizing Security Information and Event Management (SIEM) tools, Security Orchestration, Automation, and Response (SOAR) systems, and even sharpen your threat hunting skills.But this course goes beyond mere certification preparation – it's a pathway to professional growth. Uncover diverse career opportunities in cybersecurity, discover the secrets to building a successful security operations career, and understand the power of continuous learning and development.Join us on this enriching voyage, where you'll emerge not only as a certified Microsoft SC-200 professional but also as a guardian of digital resilience, ready to defend against evolving threats and contribute effectively to the world of security operations."I hope to see you in this "Microsoft SC-200 Security Operations Analyst Essentials" journey. Let's get started.Thank you.

Udemy
Get prepared for the SC-200 exam with instructor led labs and hands on simulations available 24/7 What you'll learn: Learn the concepts and perform hands on activities needed to pass the SC-200 examGain a tremendous amount of knowledge involving securing Microsoft 365 and Azure ServicesGet loads of hands on experience with Security Operations for Microsoft 365Utilize hands on simulations that can be access anytime, anywhere! We really hope you'll agree, this training is way more then the average course on Udemy! Have access to the following:Training from an instructor of over 20 years who has trained thousands of people and also a Microsoft Certified TrainerLecture that explains the concepts in an easy to learn method for someone that is just starting out with this materialInstructor led hands on and simulations to practice that can be followed even if you have little to no experienceTOPICS COVEREDINCLUDINGHANDSONLECTUREANDPRACTICETUTORIALS:IntroductionWelcome to the courseUnderstanding the Microsoft EnvironmentFoundations of Active Directory DomainsFoundations of RAS, DMZ, and VirtualizationFoundations of the Microsoft Cloud ServicesDONT SKIP: The first thing to know about Microsoft cloud servicesDONT SKIP: Azure AD is now renamed to Entra IDQuestions for John ChristopherOrder of concepts covered in the coursePerforming hands on activitiesDONT SKIP: Using Assignments in the courseCreating a free Microsoft 365 AccountActivating licenses for Defender for Endpoint and VulnerabilitiesGetting your free Azure creditConfigure settings in Microsoft Defender XDRIntroduction to Microsoft 365 DefenderConcepts of the purpose of extended detection and response (XDR)Microsoft Defender and Microsoft Purview admin centersConcepts of Microsoft SentinelConcepts of management with Microsoft Defender for EndpointManage assets and environmentsSetup a Windows 11 virtual machine endpointEnrolling to Intune for attack surface reduction (ASR) supportOnboarding to manage devices using Defender for EndpointA note about extra features in your Defender for EndpointIncidents, alert notifications, and advanced feature for endpointsReview and respond to endpoint vulnerabilitiesRecommend attack surface reduction (ASR) for devicesConfigure and manage device groupsOverview of Microsoft Defender for CloudIdentify devices at risk using the Microsoft Defender Vulnerability ManagementManage endpoint threat indicatorsIdentify unmanaged devices by using device discoveryDesign and configure a Microsoft Sentinel workspacePlan a Microsoft Sentinel workspaceConfigure Microsoft Sentinel rolesDesign and configure Microsoft Sentinel data storage, log types and log retentionIngest data sources in Microsoft SentinelIdentify data sources to be ingested for Microsoft SentinelConfigure and use MS Sentinel connectors, Azure Policy & diagnostic settingsConfigure Microsoft Sentinel connectors for MS 365 Defender & Defender for CloudDesign and configure Syslog and Common Event Format (CEF) event collectionsDesign and configure Windows security event collectionsConfigure threat intelligence connectorsCreate custom log tables in the workspace to store ingested dataConfigure protections in Microsoft Defender security technologiesPlan and configure Microsoft Defender for Cloud settingsConfigure Microsoft Defender for Cloud rolesAssess and recommend cloud workload protection and enable plansConfigure automated onboarding of Azure resourcesConnect multi-cloud resources by using Environment settingsConfigure detection in Microsoft Defender XDRSetup a simulation lab using Microsoft 365 DefenderRun an attack against a device in the simulation labManage incidents & automated investigations in the Microsoft 365 Defender portalRun an attack simulation email campaign in Microsoft 365 DefenderManage actions and submissions in the Microsoft 365 Defender portalIdentify threats by using Kusto Query Language (KQL)Identify and remediate security risks by using Microsoft Secure ScoreAnalyze threat analytics in the Microsoft 365 Defender portalConfigure and manage custom detections and alertsConfigure detections in Microsoft SentinelConcepts of Microsoft Sentinel analytics rulesConfigure the Fusion ruleConfigure Microsoft security analytics rulesConfigure built-in scheduled query rulesConfigure custom scheduled query rulesConfigure near-real-time (NRT) analytics rulesManage analytics rules from Content hubManage and use watchlistsManage and use threat indicatorsRespond to alerts and incidents in the Microsoft Defender portalUsing polices to remediate threats with Email, Teams, SharePoint & OneDriveInvestigate, respond, and remediate threats with Defender for Office 365Understanding data loss prevention (DLP) in Microsoft 365 DefenderImplement data loss prevention policies (DLP) to respond and alertInvestigate & respond to alerts generated by data loss prevention (DLP) policiesUnderstanding insider risk policiesGenerating an insider risk policyInvestigate and respond to alerts generated by insider risk policiesDiscover and manage apps by using Microsoft Defender for Cloud AppsIdentify, investigate, & remediate security risks by using Defender for Cloud AppsRespond to alerts and incidents identified by Microsoft Defender for EndpointConfigure User and Entity Behavior Analytics settingsInvestigate threats by using entity pagesConfigure anomaly detection analytics rulesInvestigate Microsoft 365 activitiesUnderstanding unified audit log licensing and requirementsSetting unified audit permissions and enabling supportInvestigate threats by using unified audit LogInvestigate threats by using Content SearchPerform threat hunting by using Microsoft Graph activity logsRespond to incidents in Microsoft SentinelConfigure an incident generationTriage incidents in Microsoft SentinelInvestigate incidents in Microsoft SentinelRespond to incidents in Microsoft SentinelInvestigate multi-workspace incidentsImplement and use Copilot for SecurityWhat is Copilot for Security?Onboarding Copilot for SecurityCreate and use promptbooksManage sources for Copilot for Security, including plugins and filesManage permissions and roles in Copilot for SecurityMonitor Copilot for Security capacity and costIdentify threats and risks by using Copilot for SecurityInvestigate incidents by using Copilot for SecurityConfigure security orchestration, automation, and response (SOAR) in Microsoft SentinelCreate and configure automation rulesCreate and configure Microsoft Sentinel playbooksConfigure analytic rules to trigger automation rulesTrigger playbooks from alerts and incidentsHunt for threats by using Microsoft Defender XDRIdentify threats by using Kusto Query Language (KQL)Interpret threat analytics in the Microsoft Defender portalCreate custom hunting queries by using KQLHunt for threats by using Microsoft SentinelAnalyze attack vector coverage by using MITRE ATT&CK in Microsoft SentinelCustomize content gallery hunting queriesCreate custom hunting queriesUse hunting bookmarks for data investigationsMonitor hunting queries by using LivestreamRetrieve and manage archived log dataCreate and manage search jobsRespond to alerts and incidents in Microsoft Defender for CloudSet up email notificationsCreate and manage alert suppression rulesDesign and configure workflow automation in Microsoft Defender for CloudGenerate sample alerts and incidents in Microsoft Defender for CloudRemediate alerts and incidents by using MS Defender for Cloud recommendationsManage security alerts and incidentsAnalyze Microsoft Defender for Cloud threat intelligence reportsCreate and configure Microsoft Sentinel workbooksActivate and customize Microsoft Sentinel workbook templatesCreate custom workbooksConfigure advanced visualizationsConclusionCleaning up your lab environmentGetting a Udemy certificateBONUS Where do I go from here?

Udemy
Security Operations Analyst, SC-200, Azure Sentinel, Microsoft sentinel, Microsoft Defender for Cloud Apps,Microsoft 365 What you'll learn: Understanding the Security Operations Center with Microsoft 365 DefenderLearning Manage alerts, incidents, and investigate security incidents with Microsoft 365 DefenderAnalyze threat analytics and detect risks with Azure AD Identity ProtectionLearn how to detect threats with Conditional Access App ControlUnderstand the Data loss prevention alerts, Microsoft Defender for Cloud Apps: Investigate data loss prevention alerts Master course in Microsoft SC-200: Microsoft Security Operations Analyst : In addition to collaborating with organizational stakeholders, the Microsoft security operations analyst ensures the security of information technology systems for the organization. They're working on reducing organizational risk by quickly resolving active attacks, improving threat protection practices, and referring violations of organizational policies to the right people. Providing secure IT systems is the responsibility of the Microsoft Security Operations Analyst. To accomplish this goal, they have to work with stakeholders in the organization. By identifying active attacks in the environment and amending them promptly, they decrease the risk of violations of organizational policies. You can get advice on how to improve threat protection.Manage, monitor, and respond to threats across their environment using a variety of security solutions. Utilizing Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products, the role investigates, responds to, and hunts for threats. These tools are also configured and deployed by the security operations analyst, because they consume operational output. You can learn the concepts and process of Security Operations Analyst, SC-200, Azure Sentinel, Microsoft sentinel, Microsoft Defender for Cloud Apps and Microsoft 365 Defender.Monitoring and Responding to Security Incidents: Understanding how to detect, investigate, and respond to security incidents within a Microsoft cloud environment. This involves using various tools and technologies to identify potential threats and take appropriate action.Implementing and Managing Detection Solutions: Learning about different security detection solutions available in Microsoft's ecosystem and how to implement and manage them effectively. This may include technologies such as Azure Sentinel, Microsoft Defender for Endpoint, etc.Managing and Investigating Security Alerts: Gaining knowledge on handling security alerts generated by various security solutions and conducting thorough investigations to determine the scope and impact of potential incidents.Implementing Threat Protection: Learning to implement and manage threat protection measures to safeguard the cloud environment from various cyber threats, such as malware, phishing attacks, etc.Securing Identities and Access: Understanding how to protect identities, manage access controls, and implement multi-factor authentication to prevent unauthorized access.Managing Cloud Security Posture: Learning about best practices for maintaining a secure cloud environment, including configuring security policies, network security, and access controls.Data Security and Privacy: Understanding data protection mechanisms and privacy regulations relevant to the Microsoft cloud environment.Governance, Risk, and Compliance: Gaining knowledge of governance frameworks, risk assessment methodologies, and compliance standards in the context of cloud security operations.Security Reports and Documentation: Learning to generate security reports and maintain documentation of security operations activities.This role needs candidates who are familiar with attack vectors, cyberthreats, incident management, and Kusto Query Language (KQL). It's also a plus if candidates know Microsoft 365 and Azure.In this master course, I would like to teach the 5 Major topics,1. Security Operations Center with Microsoft 365 Defender2. Manage alerts, incidents, and investigate security incidents with Microsoft 365 Defender3. Analyze threat analytics and detect risks with Azure AD Identity Protection4. How to detect threats with Conditional Access App Control5. Data loss prevention alerts, Microsoft Defender for Cloud Apps: Investigate data loss prevention alerts

Coursera
This course provides a comprehensive understanding of cybersecurity operations and Microsoft security technologies, integrating fundamental concepts with advanced threat detection, remediation, and automation tools. You will explore core principles of Microsoft Defender XDR, Microsoft Sentinel, and Azure security solutions, learning how to investigate, respond to, and mitigate cyber threats effectively. The course emphasizes hands-on knowledge, guiding learners through real-world security scenarios to build resilient solutions. Divided into multiple modules, it offers approximately 8:30–9:30 hours of video lectures, blending theory with practical application. The course is divided into 5 Modules, each further divided into lessons. To test learners' understanding, every module includes Assignments in the form of Quizzes and In-Video Questions. Module 1: Microsoft Defender XDR Module 2: Microsoft Defender for Endpoint Module 3: Microsoft Sentinel Module 4: Microsoft Defender and Sentinel: Unified Security Operations & Exposure Management Module 5: Microsoft Sentinel: Threat Hunting Services Module 6: Microsoft Security Copilot This course is ideal for anyone seeking a foundational understanding of Microsoft security operations tools and techniques, including security operations center (SOC) analysts, IT security professionals, and cloud security engineers looking to enhance their capabilities in threat protection and incident response using Microsoft Defender and Sentinel. By the end of this course, a learner will be able to - Understand how to detect, investigate, and respond to threats using Microsoft Defender and Sentinel. - Describe the core capabilities and benefits of Microsoft Defender XDR. - Explore methods to protect managed and unmanaged devices using Microsoft Defender and Azure Arc. - Perform threat hunting, automated remediation, and security optimization using KQL and Sentinel tools. - Implement Microsoft Security Copilot to enhance analyst efficiency and decision-making.
YouTube
Learn about the essential responsibilities and key roles of a Security Operations Center (SOC) Analyst in this 21-minute video. Explore the fundamental aspects of threat detection and real-time monitoring of network traffic and system logs, understanding how SOC Analysts utilize advanced tools and technologies to identify anomalies and evaluate incident severity. Discover the incident response procedures SOC Analysts follow, including team coordination for threat containment and risk mitigation. Gain insights into proactive security measures such as vulnerability assessments and security enhancement recommendations that form crucial parts of a SOC Analyst's daily duties.
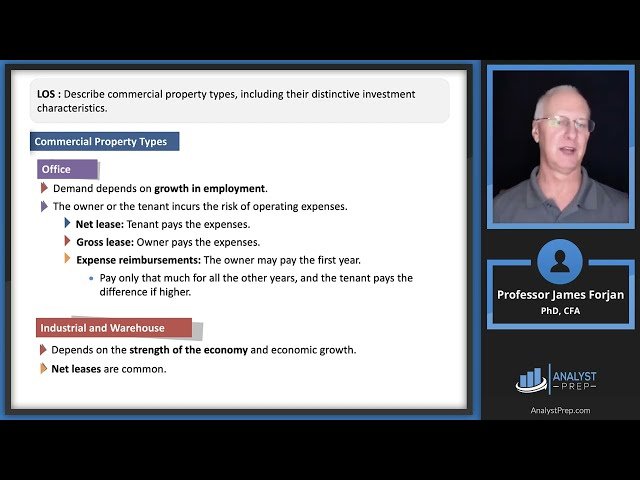
YouTube
Learn about real estate investment fundamentals in this educational video designed for CFA Level II exam preparation, covering essential topics like private and public real estate investments, property classifications, portfolio roles, and economic value determinants. Explore different commercial property types and their unique investment characteristics while understanding the due diligence process for both private and public equity investments. Master concepts related to residential and non-residential properties, liquidity considerations, cash flow contributors, and economic growth factors that influence real estate investments. Gain insights into real estate investment indexes, their construction methodology, potential biases, and the impact of appraisal lag on valuations. Develop a comprehensive understanding of why investors choose real estate as an asset class and how various factors contribute to property values and investment performance.

Swayam
Learn fundamental investment principles and financial analysis techniques through this 8-week course from the Indian Institute of Management Bangalore. Begin with investment fundamentals and the relationship between risk and return, then explore fixed income securities and their valuation methods. Analyze equity investments through various valuation models and financial statement analysis techniques. Discover derivatives markets by studying forwards and futures contracts, their pricing mechanisms, and hedging applications. Master portfolio theory concepts including diversification, efficient frontier construction, and optimal portfolio selection using modern portfolio theory. Examine financial planning strategies and understand the impact of taxation on investment decisions and portfolio management. Conclude with a comprehensive review that integrates all investment concepts and their practical applications in real-world financial decision-making scenarios.

Corporate Finance Institute
Cash Flow Cycles and Analysis Course Overview In this Cash Flow Cycles and Analysis course, we look at how companies manage their cash flow. We will explore both the operating cash flow cycle and the investing cash flow cycle. We use real-world examples to calculate a company’s working capital funding gap. Then we will go over important strategies companies can use to optimize their working capital accounts. From there we will look at the longer-term investments such as sustaining or expansionary capital expenditures. We will assess the payback time on a project and look at the return on investment. In the end, we’ll combine what we learned and produce a cash flow statement to compare key metrics such as net income, EBITDA, cash flow from operations, and free cash flow. Throughout the course, we’ll be looking at things from both the lender’s perspective and the borrower’s perspective so you’ll have a full picture as a complete credit analyst of how to forecast and optimize cash flow for a business. Cash Flow Cycles and Analysis Learning Objectives Upon completing this course, you will be able to: Discuss the difference between a company’s short-term operating cash flow and long-term investing cash flowCompare working capital objectives and capital investment objectivesCalculate working capital funding gap, investment payback and return on investmentUse a company’s financial statement to conduct a cash flow analysis and compare key metrics Who should take this course? This Cash Flow Cycles and Analysis course is perfect for any aspiring credit analysts working in insurance, underwriting, rating agencies, commercial lending, corporate credit analysis, and other areas of credit evaluation.

FutureLearn
Master essential business analysis skills and tools for industry success Gain a practical introduction to business analysis on this two-week course designed for professionals ready to transition into or enhance their skills in this essential field. Understand the role of a business analyst in modern organisations Start your journey by exploring the function of business analysis in a variety of project settings. You’ll learn how business analysts contribute to successful project outcomes by identifying problems, clarifying business needs, and guiding informed decisions. Whether you work in IT, finance, marketing, or operations, you’ll see how analysis plays a key role in aligning solutions with strategic goals. Apply structured techniques to analyse business problems Put analysis into action by learning core techniques like SWOT, MOST, and PESTLE. Use visual tools like flowcharts and BPMN to model processes and map out how business functions operate. You’ll get to practise drafting user stories, writing clear requirement statements, and building simple business cases that communicate value and feasibility. Engage stakeholders and gather requirements effectively Strong communication is critical for any analyst. In this section, you’ll learn how to identify and engage stakeholders through stakeholder mapping and how to elicit and validate requirements that align with organisational priorities. Through optional hands-on exercises, you’ll practise turning real-world challenges into actionable insights that drive project success. This course is ideal for early-career professionals and current analysts, as well as project managers, IT staff, or those in operations or marketing looking to step into a business analysis role or prepare for certification.

LinkedIn Learning
Practice your skills and get ready to tackle the Microsoft Security Operations Analyst Associate (SC-200) certification exam.

YouTube
Dive into a comprehensive 45-minute video tutorial designed to prepare aspiring SOC (Security Operations Center) analysts for scenario-based interviews. Master essential topics including threat detection, incident response, and vulnerability management. Learn to effectively analyze security events, respond to incidents, and protect organizational assets. Explore real-world scenarios covering phishing email responses, threat intelligence utilization, vulnerability assessment, intrusion detection, SIEM analysis, and incident communication. Gain valuable insights on enhancing problem-solving skills and receive additional tips for acing job interviews. Whether you're a beginner or looking to refine your skills, acquire practical knowledge and strategies to excel in your next SOC analyst interview.

