Courses
Discover thousands of courses from top institutions and platforms worldwide
Level
Course Type
Duration

YouTube
Discover the profound connection between childhood stressors and adult behaviors in this insightful 13-minute TEDx talk. Explore the concept of "Demons & Drivers" and learn how to harness the power of your past experiences to fuel your life's purpose. Gain valuable insights into transforming personal challenges into catalysts for growth and success. Uncover strategies for identifying and leveraging your defining driver to overcome obstacles and achieve your goals. This thought-provoking presentation offers a unique perspective on personal development and empowerment, encouraging viewers to embrace their inner demons and channel them towards positive change.

YouTube
Learn about the Driver Risk Scores (DRS) threat detection system in this conference talk from BSidesCharm 2024. Explore how to assess and quantify the security risks posed by device drivers through a comprehensive scoring system based on seven critical characteristics. Discover how this scoring methodology, comparable to CVE scoring, combines security features and real-world data to generate actionable insights for system administrators and security teams. Drawing from research at loldrivers.io, understand the varying levels of driver vulnerabilities and learn to make informed decisions about driver deployment in your environment. Presented by Dana Behling, a cybersecurity researcher at Carbon Black, who brings both technical expertise in digital security and a creative approach influenced by her passion for science fiction and fantasy literature.

Corporate Finance Institute
Private Banking Course OverviewPrivate banking services present many unique opportunities for a financial institution and its clientele. This Private Banking course examines what the role of a private banker entails, how their services differ from a more traditional retail banking environment, and the importance of analyzing the risk and return of a client’s investments. We discuss integrating client investment strategies with risk tolerance and financial goals to tailor personalized solutions for clientele and their families.We cover all the most important qualitative and quantitative factors that will influence private banking clients, including important risk and return calculations and the various investment strategies available. We also cover the personal financial planning process, sources of risk, and the implementation of those plans and strategies. We use an interactive video case study to help illustrate the key takeaways and to demonstrate real-world examples of clients in a private banking setting.Private Banking Learning ObjectivesUpon completing this course, you will be able to:Define the roles and responsibilities of the private banker.Explain the relationship between risk and return.Align client investment strategies with risk tolerance and financial goals.Describe the benefits and logistics of offshore banking.Design credit solutions to meet client needs and resources.Who Should Take This Course?This course is designed for current and aspiring commercial banking professionals, including relationship managers or loan officers, credit analysts, loan brokers, and adjudicators. This course will prepare you with the knowledge to properly assess various borrowing requests for these unique business borrowers.
YouTube
A 44-minute talk by Wen Wei Ho at the Erwin Schrödinger International Institute for Mathematics and Physics (ESI) explores the concept of geometric quantum drives, with a focus on hyperbolically driven quantum systems. Delivered as part of the Thematic Programme on "Entanglement in Many-body Quantum Matter: Dynamics, Dissipation, Equilibration," this presentation investigates quantum drives beyond the conventional time-periodic (Floquet) and time-quasiperiodic modulations. Discover a theoretical framework where a classical particle moving on a smooth connected manifold steers a quantum Hamiltonian over time, creating diverse time-dependent quantum Hamiltonians whose properties depend on the underlying manifold and trajectory. Learn about "hyperbolically driven quantum systems" applied to compact 2D hyperbolic Riemann surfaces, and understand how they exhibit topologically classified responses in the adiabatic limit that can be measured through simple local observables. Gain insights into this general framework for mapping the landscape of time-dependent quantum systems, investigating their universal phase structures, and potentially enhancing modern quantum simulator capabilities.

YouTube
Watch a 46-minute research talk from Google DeepMind's Andreas Terzis exploring the intersection of differential privacy and synthetic data generation for training large language models. Delve into critical aspects of LLM development including alignment, trust mechanisms, watermarking techniques, and copyright considerations while learning about innovative approaches to maintain privacy in AI training data. Gain insights into how synthetic data can be generated with differential privacy guarantees to protect sensitive information while still producing effective training datasets for language models.

YouTube
Explore a comprehensive 6-hour golf tutorial focused on mastering the driver. Learn techniques to balance distance and accuracy, increase clubhead speed, and improve overall driving performance. Discover tips for hitting draws and fades, correcting common mistakes, and optimizing your setup. Address specific challenges faced by senior and beginner golfers, including increasing swing speed and distance. Dive into advanced concepts like swing plane, golf lag, and proper release. Gain insights on fixing slices, improving contact, and achieving an effortless swing. Utilize practical drills and exercises to enhance your driving skills and consistently hit longer, more accurate drives.

YouTube
Discover a comprehensive 90-minute tutorial on forex trading software that claims to offer a 99% profitable strategy. Learn how to utilize private forex software, implement winning strategies like heiken ashi, and potentially earn daily profits. Explore various trading techniques, including moving average combinations, and gain insights into intraday trading setups. Understand how this software aims to solve common forex trading problems and potentially increase your success rate in the foreign exchange market.

YouTube
Explore the concept of Secure Remote Access in enterprise environments through this 47-minute Black Hat conference talk. Delve into the challenges of equipping staff with mobile devices for daily tasks, examining how this increased mobility impacts workforce connectivity and security. Analyze the role of underlying operating systems and supporting solutions, particularly Virtual Private Networks (VPNs), in maintaining security for remote workers. Learn from experts Charl van der Walt and Wicus Ross as they question whether current Secure Remote Access solutions are truly effective or merely an illusion of security. Gain insights into the implicit burdens placed on staff to stay connected securely and consider the potential vulnerabilities in existing remote access systems.

YouTube
Explore the intricacies of virtual private network (VPN) security in this 41-minute Black Hat conference talk. Delve into common vulnerabilities and potential exploits associated with VPN implementations on Windows systems. Gain insights from security expert Loki as they dissect the challenges and risks inherent in VPN technologies, offering valuable knowledge for IT professionals, network administrators, and cybersecurity enthusiasts. Discover practical strategies to enhance VPN security and protect against potential threats in Windows environments.

YouTube
Explore free software options for duplicating and backing up SSDs and hard drives in this comprehensive video tutorial. Learn how to use Samsung Data Migration, DiskGenius, Clonezilla Live, and the Linux DD command to clone drives effectively. Gain practical knowledge on connecting new drives for cloning, using M.2 adapters and USB enclosures, and returning drives to factory state using the Windows DiskPart command. Discover essential tips for drive backups and find links to official software downloads, related videos, and recommended hardware. Whether you're upgrading your PC or creating backups, master the techniques for seamless drive cloning and data migration.
YouTube
Learn about private evolution convergence in this 46-minute workshop presentation delivered by Aaditya Ramdas from Carnegie Mellon University at the Paul G. Allen School. Explore the theoretical foundations and practical implications of how private evolutionary processes achieve convergence, examining the mathematical frameworks and computational methods that govern these systems. Discover the intersection of privacy-preserving techniques with evolutionary algorithms, understanding how convergence properties are maintained while protecting sensitive information throughout the evolutionary process. Gain insights into the latest research developments in this specialized field that combines differential privacy concepts with evolutionary computation theory.

YouTube
Explore how GraphQL can be used as a secure innovation boundary and driver of data-driven culture in this conference talk from NDC Sydney 2020. Discover common scenarios faced by organizations struggling with data access, integration, and security. Learn how the speakers implemented a Secure Innovation Boundary called Purple Graph to address these challenges at Telstra Purple. Gain insights into the process of pitching, prototyping, launching, and operating such a system. Understand the technical and non-technical learnings, cultural changes, and best practices for implementing similar solutions in your organization. Walk away with practical tips on leveraging GraphQL to drive innovation, improve data accessibility, and enhance security across your systems.

YouTube
Explore the power of Set Driver/Set Driven Xpresso in Cinema 4D through this 32-minute tutorial. Learn how to leverage this essential Xpresso feature to streamline your workflow and enhance your 3D projects. Discover practical examples and applications, including working with spline shaders, project time manipulation, creating shortcuts, and utilizing sweep and bend objects. Gain the knowledge to apply these techniques to your own unique workflows, even if you're new to Xpresso. Follow along with step-by-step instructions and insider tips to unlock the potential of this user-friendly yet powerful tool in Cinema 4D.

YouTube
Learn about private special situations investing through a 50-minute educational video covering key concepts for the CFA® Level III exam's Private Markets module. Master essential learning objectives including characteristics and risks of special investment situations, distressed debt features and strategies, complex investment scenarios involving financial stress, due diligence and valuation processes, and the role of special situations in strategic asset allocation. Explore how to evaluate distressed debt opportunities, understand financing alternatives for troubled issuers, and analyze risk-return profiles compared to other private debt investments. Gain practical knowledge about conducting thorough due diligence and applying appropriate valuation methods when assessing special investment situations in private markets.

Udacity
Elevate your skills in data privacy through AI techniques like Federated Learning, Differential Privacy, and Encrypted Computation. Learn to protect sensitive data while building secure, privacy-first applications.

Coursera
We are presently facing a potential extinction crisis for the order Primates (and many other life forms). In this course we will learn about threats to primate conservation globally. We will be using the, “Primates in Peril: The World’s 25 Most Endangered Primates 2018-2020” by Schwitzer et al. (2019) as a basis for the discussion of global primate populations. We will investigate conservation status, threats to conservations, success and failures within protecting our closest evolutionary cousins.

MIT OpenCourseWare
This is a three-day workshop that took place during the MIT Independent Activities Period (IAP) in January, 2019. This workshop aims to provide information for students to prepare for the FAA Private Pilot Knowledge Test. Topics include airplane aerodynamics, aircraft systems, navigation, meteorology, aircraft ownership and maintenance, aircraft performance, multi-engine and jets.

YouTube
Explore the concept of differentially private mechanisms in this 15-minute IEEE presentation. Gain insights into the principles and applications of differential privacy, a powerful technique for protecting sensitive data while allowing for meaningful analysis. Discover how these mechanisms can be learned and implemented to enhance privacy in various data-driven scenarios.

YouTube
Explore the intersection of privacy and generative AI in this 45-minute Google TechTalk presented by Tim Dockhorn from the University of Waterloo. Gain insights into Differentially Private Diffusion Models (DPDMs), a novel approach that combines the power of diffusion models with differential privacy techniques. Learn how DPDMs address the challenge of limited data in privacy-sensitive domains by generating synthetic data while preserving privacy. Discover the optimal design space for diffusion models under differential privacy constraints and understand the concept of noise multiplicity, a tailored modification of differentially private stochastic gradient descent. Delve into recent advancements that leverage public pre-training to enhance DPDM performance, offering a comprehensive overview of this cutting-edge research in machine learning and data privacy.
YouTube
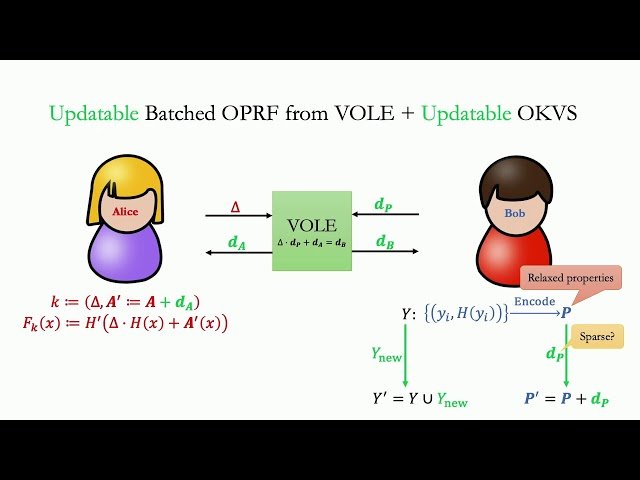
Learn about updatable private set intersection (UPSI) in this 32-minute conference talk that explores how two parties can securely compute the intersection of their private sets while supporting efficient updates over time. Discover the fundamental concepts of private set intersection (PSI), where parties can determine common elements in their datasets without revealing any additional information beyond the intersection itself. Explore how UPSI extends traditional PSI by enabling regular computations on sets that change over time, with computational costs that scale based on update sizes rather than entire dataset sizes. Examine recent developments in the field, including key theoretical results, core cryptographic techniques used in UPSI protocols, and current research directions. Gain insights into the ongoing efforts to improve efficiency and security in updatable private set intersection systems, along with understanding the significant open problems that remain in this area of secure computation research.

